This blog post provides you updated (Microsoft 365 security certification) MS-500 exam questions. By trying out these free Microsoft 365 security administrator (MS-500) questions and answers, you will learn about the security and compliance solutions which are available for Microsoft 365 and Hybrid environments.
What to expect in Microsoft 365 Security Certification?
Microsoft 365 security certification tests the capability of an individual who should be able to plan and deploy security strategies in MS 365 and hybrid environments. There are no specific ms-500 prerequisites, if you have interest and knowledge in handling Microsoft 365 security features, you can take up this certification exam.
Objectives of MS-500 (Microsoft 365 security) Certification Exam:
- Identity management and provisioning user access
- Managing Governance and Compliance features
- Information protection on Microsoft 365 environment
- Threat protection management
Let’s start learning through these exam questions and detailed explanations.
Domain : Implement and manage threat protection
Q1 : You have configured an Azure Sentinel solution and wish to proactively look for security threats using Hunting in the Sentinel Portal. Which query language must you use when searching for threats?
A. Transact-SQL
B. Gremlin query language
C. MySQL
D. Kusto query language
Correct Answer: D
Explanation:
Hunting in Azure Sentinel is based on Kusto query language. This is a read-only request to process data and return results. The request is stated in plain text, using a data-flow model designed to make the syntax easy to read, author, and automate. designed to make the syntax easy to read, author, and automate.
Option A is incorrect. T-SQL (Transact-SQL) is a set of programming extensions from Sybase and Microsoft that add several features to the Structured Query Language. Some of the tools that use T-SQL are SQL Server Management Studio, Azure Data Studio, SQL Server Data Tools and sqlcmd.
Option B is incorrect. Gremlin is a query language used to retrieve data from and modify data in the applications graph. Azure Cosmos DB supports Gremlin.
Option C is incorrect. MySQL is an open source relational database management system with a client-server model. Azure Database for MySQL supports MySQL.
Reference: To know more about Azure Sentinel Hunting, please refer to the link below: https://docs.microsoft.com/nb-no/azure/sentinel/hunting
Domain : Implement and manage threat protection
Q2 : As a step to harden your Office 365 security you wish to run Microsoft Office 365 Attack simulator. You configure Microsoft Defender Advanced Threat Protection and assign your users Microsoft 365 Enterprise E5 licenses. What must be configured to run the attack simulator?
A. Create Conditional Access session control scoped at Office 365
B. Assign your users Defender plan 2-licenses
C. Configure an identity protection user risk-policy
D. Enable multi-factor authentication
Correct Answer: D
Explanation:
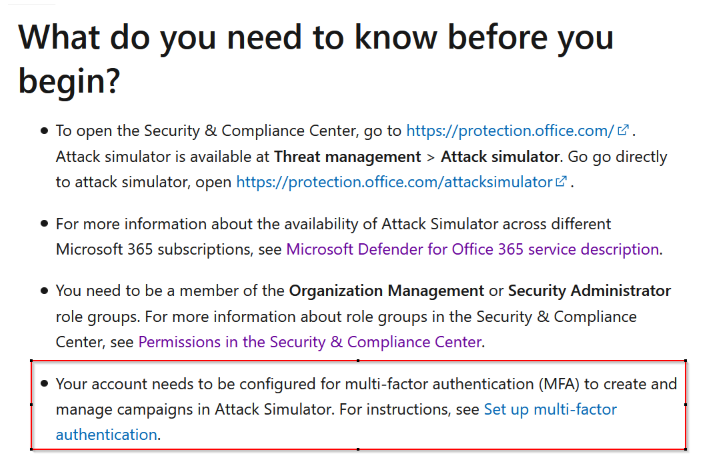
Enabling MFA is a prerequisite for running Microsoft Attack Simulator.
Since the answer is given in the documentation, the other options are incorrect.
Reference: To know more about Microsoft Office 365 Attack Simulator, please refer to the link below: https://docs.microsoft.com/en-us/microsoft-365/security/office-365-security/attack-simulator?view=o365-worldwide
Domain : Implement and manage threat protection
Q3 : You are an IT administrator in a hybrid environment consisting of Windows 10 devices. Most of your users have migrated their mailboxes to Exchange online, but Sales and Marketing still have their mailboxes on premise. All users are assigned Microsoft 365 Enterprise E5 licenses. You wish to take advantage of the security capabilities in Microsoft Defender Advanced Threat Protection, and plan to run the Microsoft Office 365 Attack simulator on users in the Marketing-department. You have enabled MFA for all users. What must you do?
A. Migrate the Marketing group members to Exchange Online
B. Set AD Connect in staging mode
C. Create a mail-enabled security-group and add the Marketing group members
D. Configure the on-premise public IP in the MFA “trusted IP” settings
Correct Answer: A
Explanation:
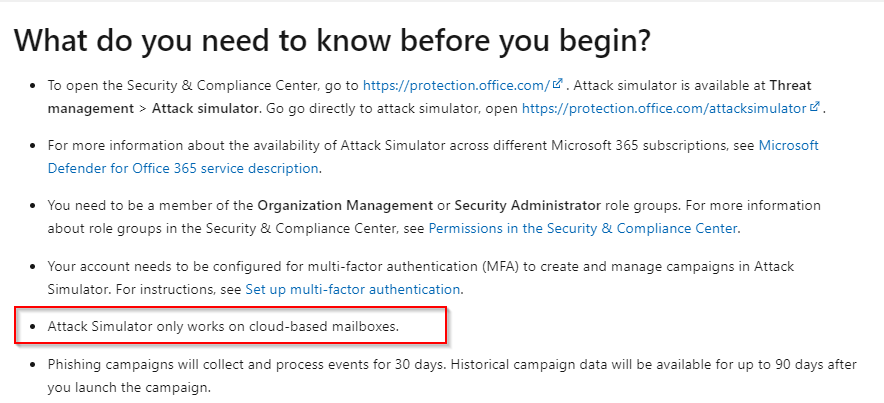
Attack Simulator only works on cloud-based mailboxes.
Since the answer is clearly stated in the documentation, all other options are incorrect.
Reference: To know more about Microsoft Office 365 Attack Simulator, please refer to the link below: https://docs.microsoft.com/en-us/microsoft-365/security/office-365-security/attack-simulator?view=o365-worldwide
Domain :Implement and manage threat protection
Q4 : You are responsible for securing your organizations Exchange online environment. To help prevent impersonation attacks, you wish to enable artificial intelligence (AI) as a policy for all users. What should you configure?
A. Litigation Hold
B. Security defaults
C. Mailbox intelligence
D. Safe attachment policy
Correct Answer: C
Explanation:
Mailbox intelligence uses the mailbox’s normal traffic patterns to better enable the impersonation detection to catch unusual messages. It is able to recognize if an email is coming from an impersonator and flag it. For example, if you usually receive emails from [email protected] and an email comes in from an impersonator with the address [email protected], the system will recognize that this is not the correct email address and flag the email.
Option A is incorrect. This is a notification sent from an organization’s legal team to employees instructing them not to delete electronically stored information that may be relevant to a legal case.
Option B is incorrect. This is a free security baseline offered by Microsoft.
Option D is incorrect. This is a policy to protect against malicious attachments.
Reference: To know more about Mailbox Intelligence and other anti-phishing methods, please refer to the link below: https://docs.microsoft.com/en-us/microsoft-365/security/office-365-security/set-up-anti-phishing-policies?view=o365-worldwide
Domain : Implement and manage threat protection
Q5 : You have a Microsoft 365 subscription and have assigned Microsoft 365 E5 licenses to your users. Some of your users have issues with their exchange online mailboxes, so you submit a support ticket to Microsoft. You want to ensure that Microsoft cannot access your content to perform service operations without your approval. The solution should allow Microsoft Engineers to make a data access request for a limited amount of time. From the Microsoft 365 admin center, what should you enable?
A. Customer Lockbox
B. Whiteboard
C. Privacy profile
D. Bing data collection
Correct Answer: A
Explanation:
Office 365 Customer Lockbox is a feature which enables customers to control how a Microsoft support engineer is going to access customer data when investigating and troubleshooting some service issues related to customers Office 365 tenant. This is typically after the customer has raised a ticket with Office 365 Support.
Option B is incorrect. This service allows users in your organization to use Microsoft Whiteboard and collaborate on shared whiteboards.
Option C is incorrect. This service lets you set the privacy statement of your organization.
Option D is incorrect. This service lets you choose whether Bing can learn from your organization’s search behavior to better its results.
Reference: To know more about Customer Lockbox, please refer to the link below: https://docs.microsoft.com/en-us/microsoft-365/compliance/customer-lockbox-requests?view=o365-worldwide
Domain : Implement and manage information protection
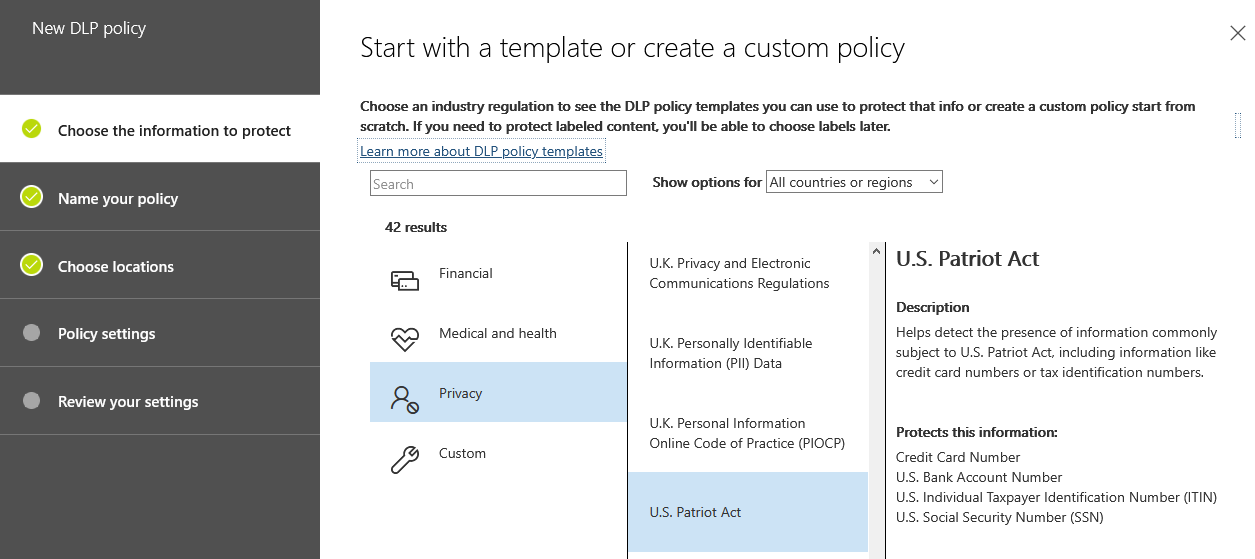
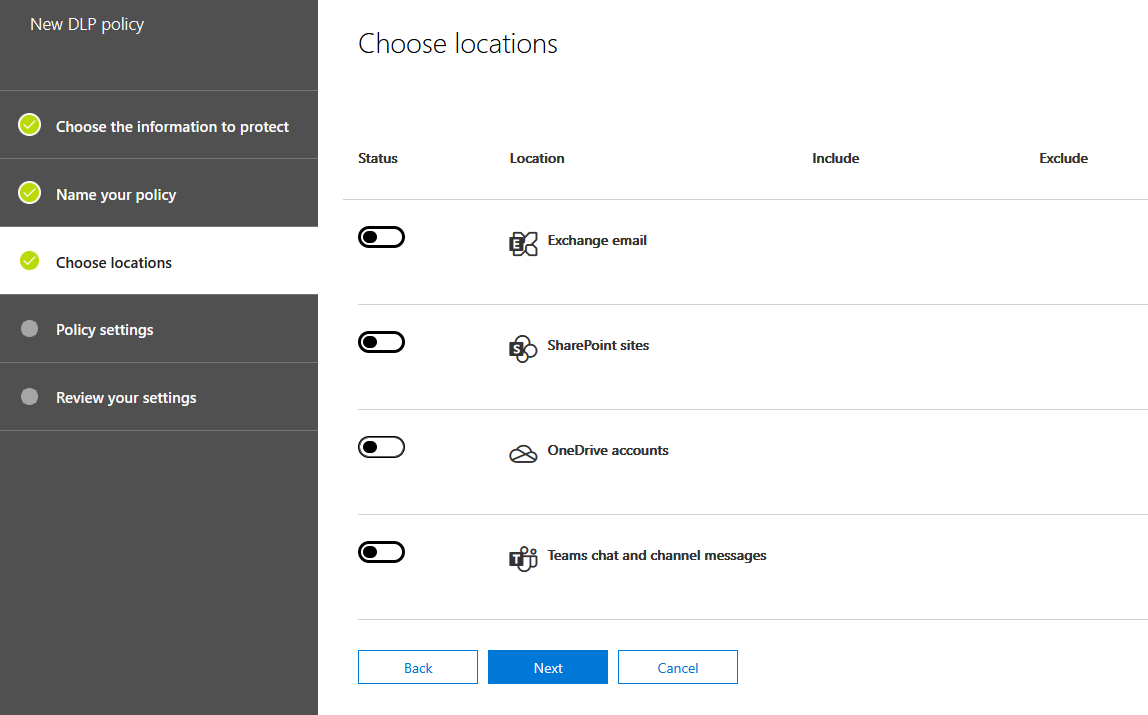
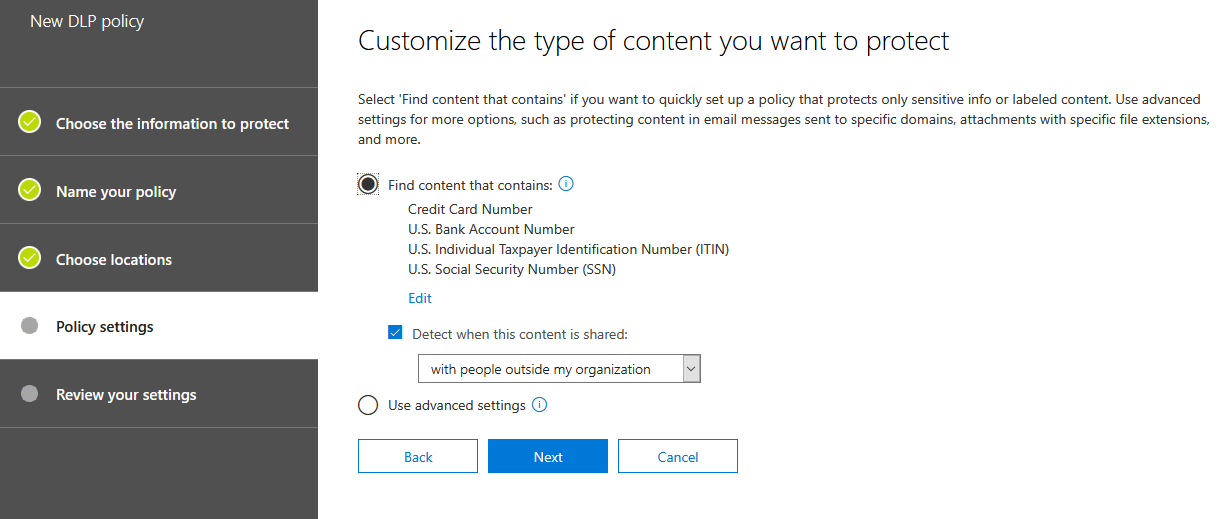
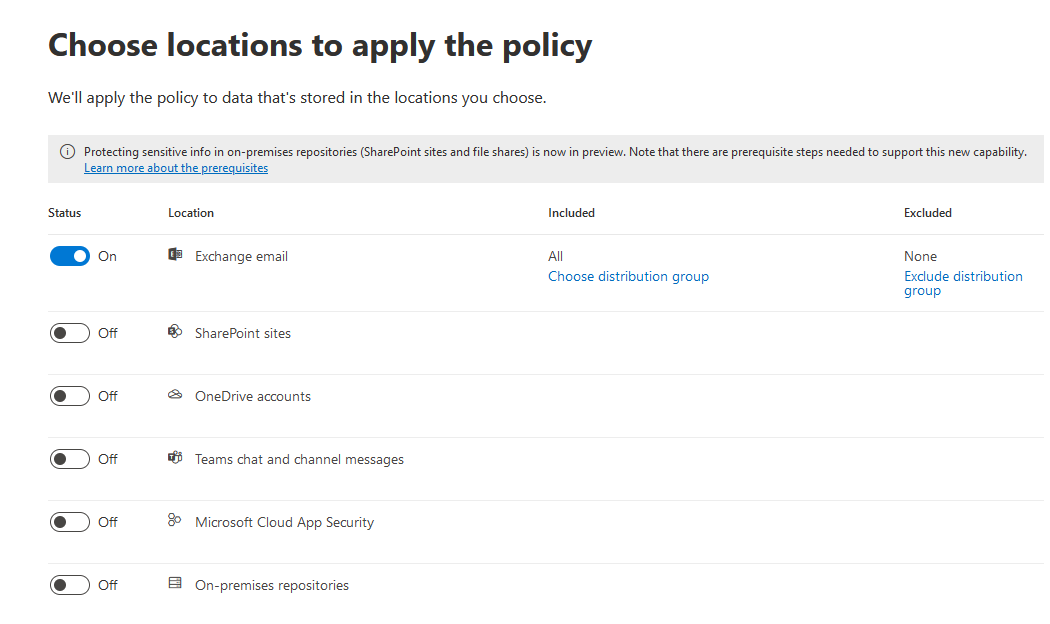
Q6 : You have a configured a data loss prevention (DLP) with the following settings:





After implementing the policy, your users are reporting that they can still send credit card number information out of the organization by mail. What must you change to ensure that the policy works as intended (stop information within the U.S. Patriot Act from being shared outside of the organization)?
A. Encrypt email messages (applies only to content in Exchange)
B. Locations
C. Choose the information to protect
D. Let people who see the tip override the policy
Correct Answer: B
Explanation:
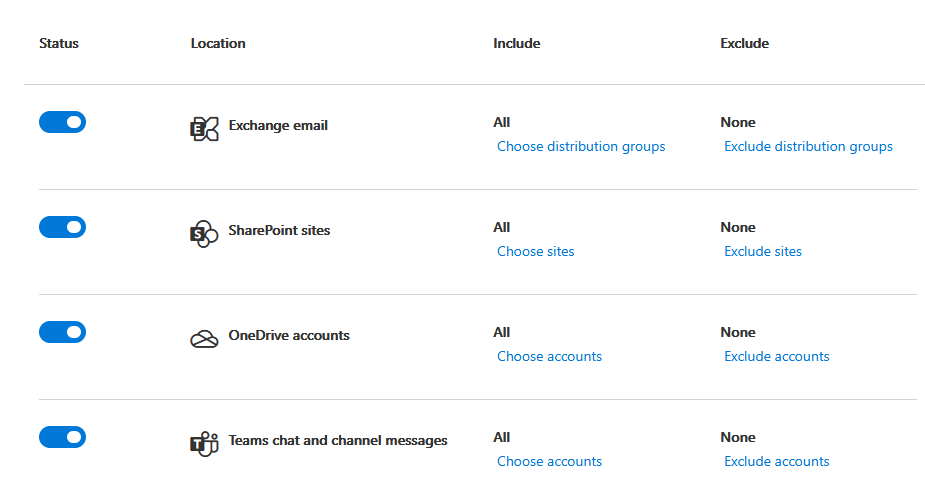
In this policy all locations are disabled: Exchange email, SharePoint sites, OneDrive Accounts, Teams chat and channel messages.
You must enable the location of the service you want to impact:
Since the answer is given in the documentation, the other options are incorrect.
Reference: To know more about implementing DLP policies, please refer to the link below: Create, test, and tune a DLP policy – Microsoft 365 Compliance | Microsoft Docs
Domain : Implement and manage information protection
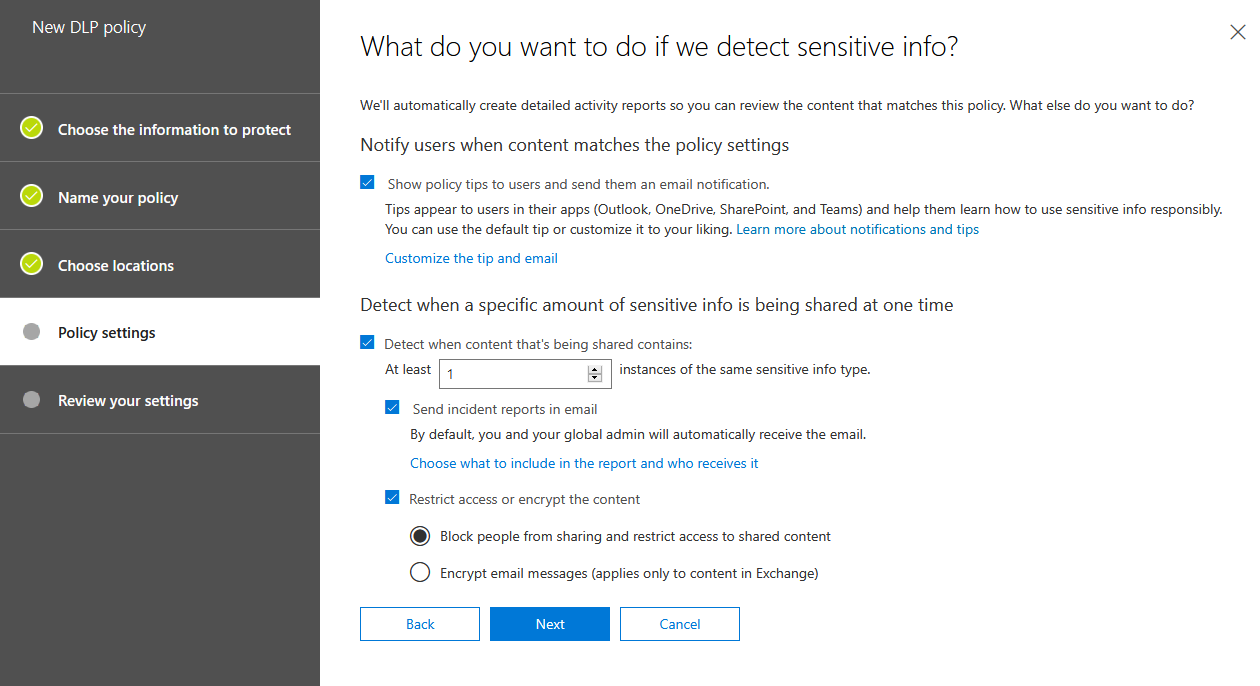
Q7 : You are a global administrator in an organization with a Microsoft 365 subscription. You want to protect the information that is being shared both inside and outside of your organization, so you decide to create Data Loss Prevention policies.
Your company has a big customer base in France, and you want to make sure email containing France National ID Card information cannot be sent out of your organization. Administrator and the user who is sending the email must be notified when rule match occurs.
For security reasons you would also like the administrator to be notified whenever someone emails Azure Storage Account Key information within your organization. The user sending the Storage Account Key information must also be notified when rule match occurs.
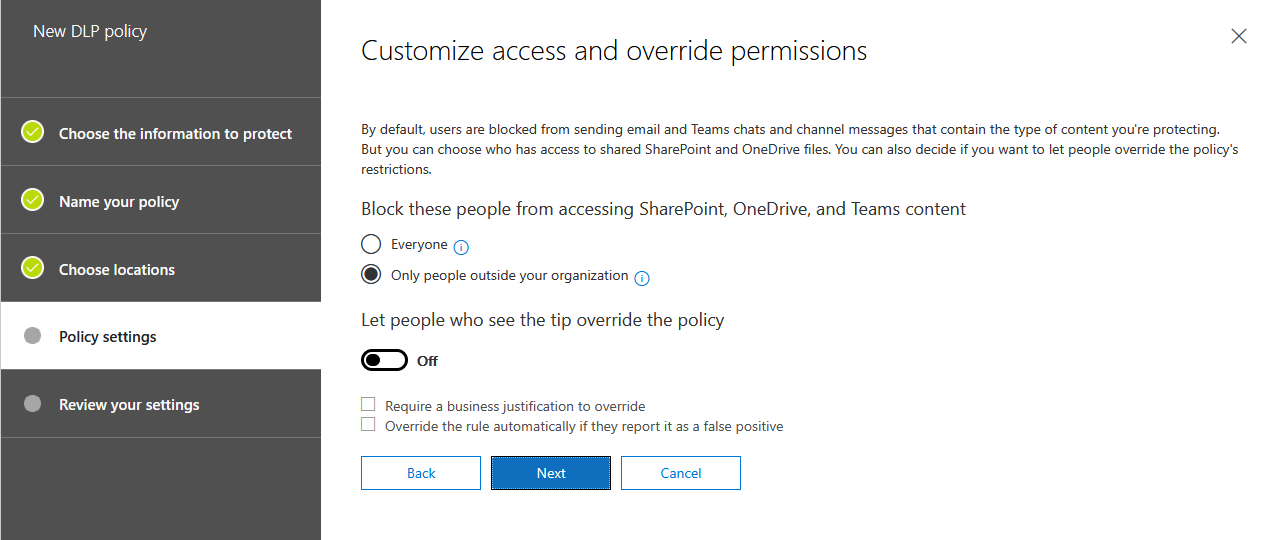
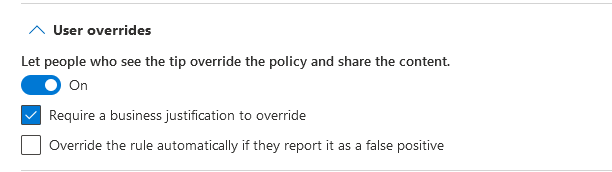
You want to restrict users from sharing SWIFT Code from OneDrive outside of your organization, but also enable users to override the policy if needed. Users must state a business justification if they choose to override the policy.
Lastly you would like the administrator to be notified whenever someone is sharing a .exe file from OneDrive within your organization. The users sending and receiving the file must not be notified.
What is the minimum number of policies and rules needed to achieve this?
A. 1 policy, 2 rules
B. 2 policy, 2 rules
C. 2 policy, 3 rules
D. 2 policies, 4 rules
E. 3 policies, 2 rules
F. 3 policies, 3 rules
Correct Answer: D
Explanation:
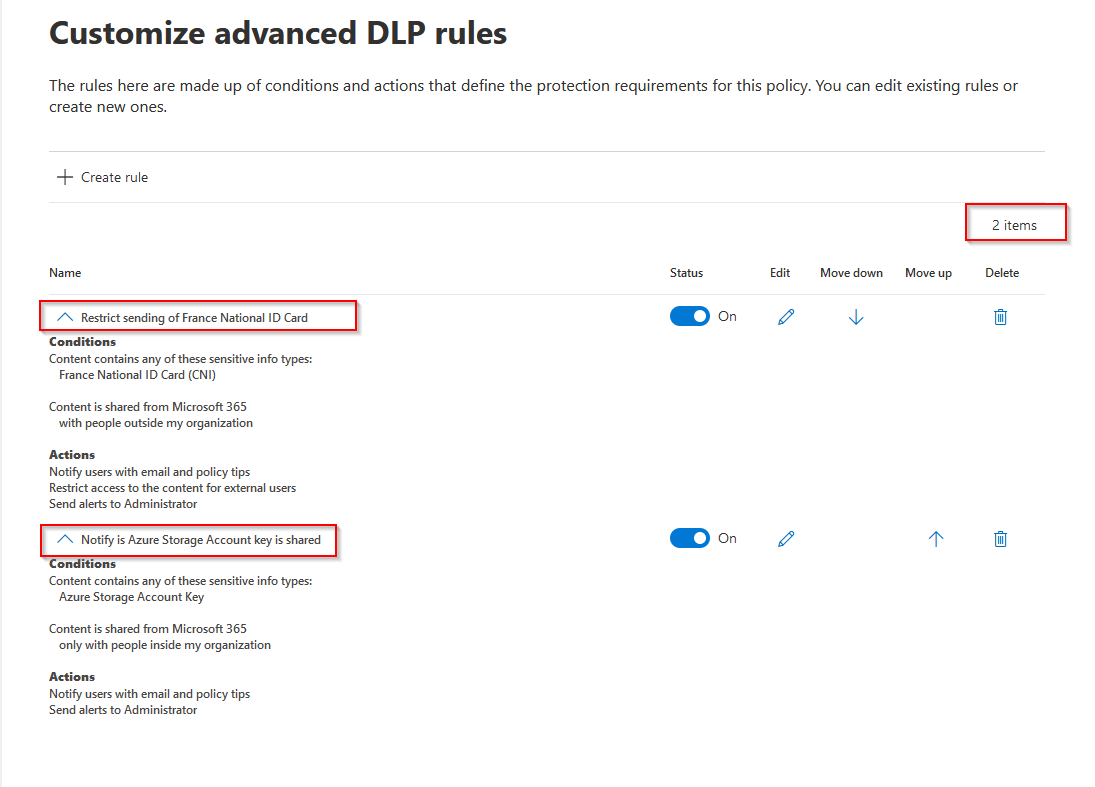
You need to create two DLP policies; one for Exchange (Policy 1) and one for OneDrive (Policy 2).
Within Policy 1 you must create two rules;
First one for stopping mail containing France National ID Card information from being sent outside the organization.
Second one for notifying the administrator and end user when they send mail containing Azure Storage Account Key information.
For both rules you select notify end user and administrator
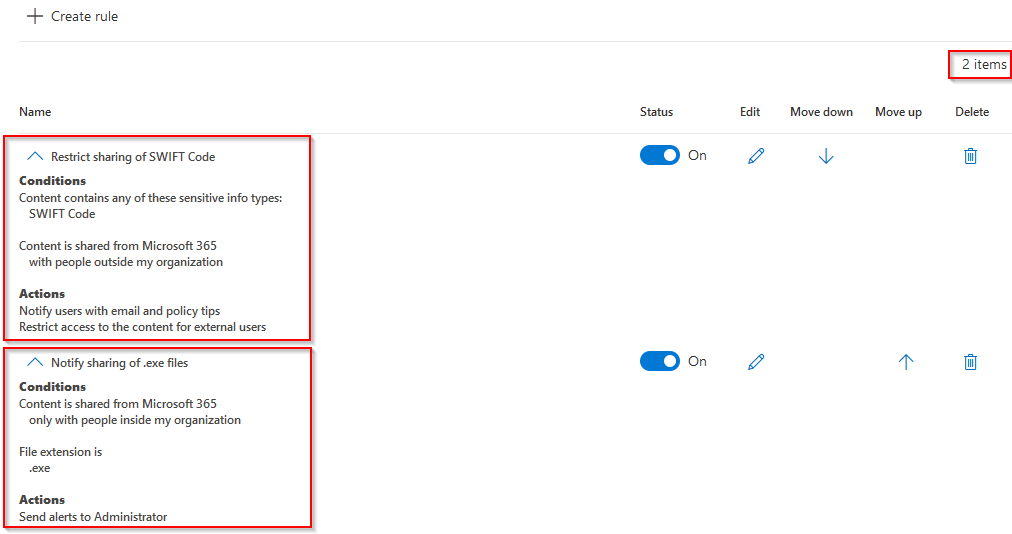
Within Policy 2 you must create two rules;
First one for restricting sharing of SWIFT Code outside of your organization. Set the details as shown in the exhibit below.
Second one for notifying administrators when .exe files are being shared within your organization. Set the details as shown in the exhibit below.
Policy 1:
Policy 2:
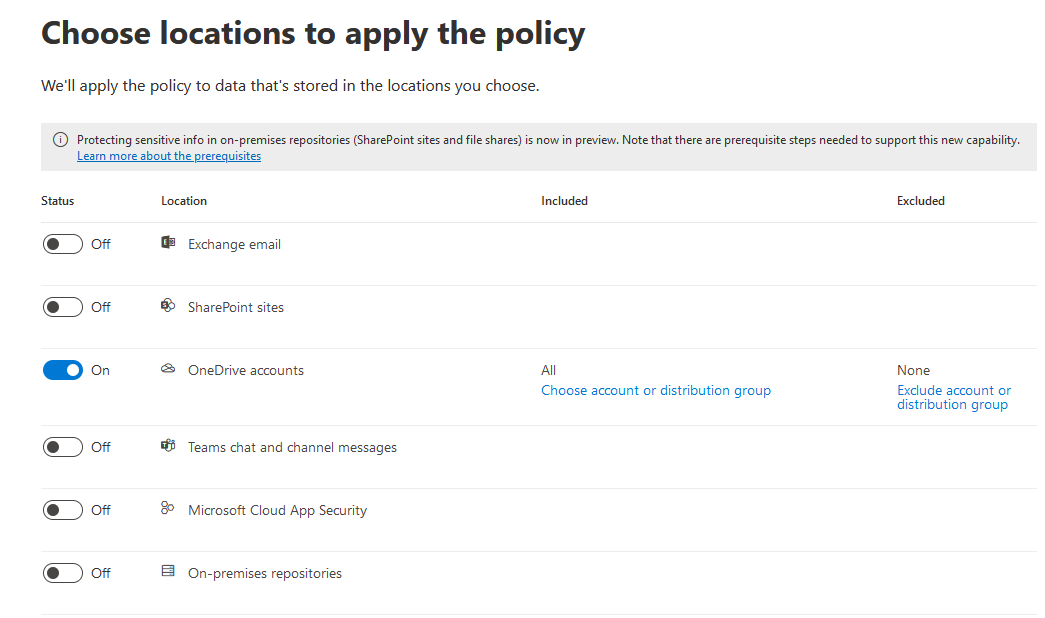
Details “Restrict sharing of SWIFT Code”:
Since the answer is given in the documentation, the other options are incorrect.
Reference: To know more about DLP policies, please refer to the link below: https://docs.microsoft.com/en-us/microsoft-365/compliance/data-loss-prevention-policies?view=o365-worldwide
Domain : Manage governance and compliance features in Microsoft 365
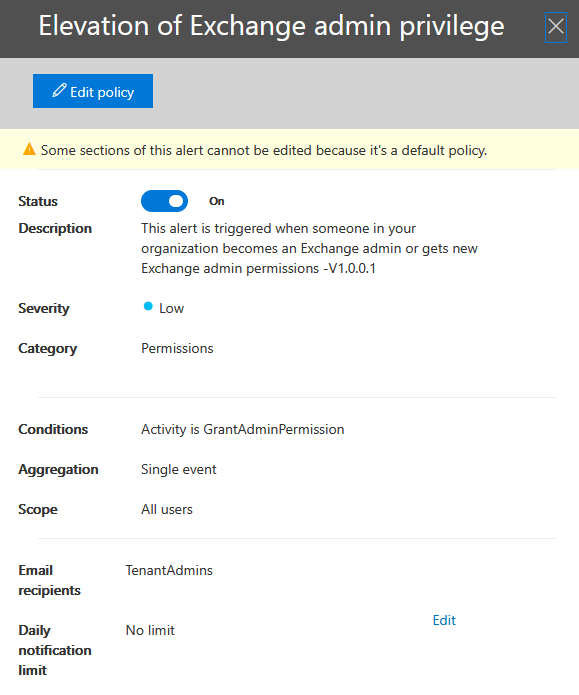
Q8 : You are the IT administrator of an organization with a Microsoft 365 subscription. You need to be notified by email whenever someone is assigned administrative permissions in your Exchange Online organization. How would you configure this from the Security & Compliance admin center?
A. From Search & investigation, create an eDiscovery case
B. From Data privacy, create a Data subject request
C. From Records management, create an Event
D. From Alerts, create an alert policy
Correct Answer: D
Explanation:
You need to create an alert policy for Elevation of Exchange admin privilege.
When enabled the policy generates an alert when someone is assigned administrative permissions in your Exchange Online organization. For example, when a user is added to the Organization Management role group in Exchange Online.
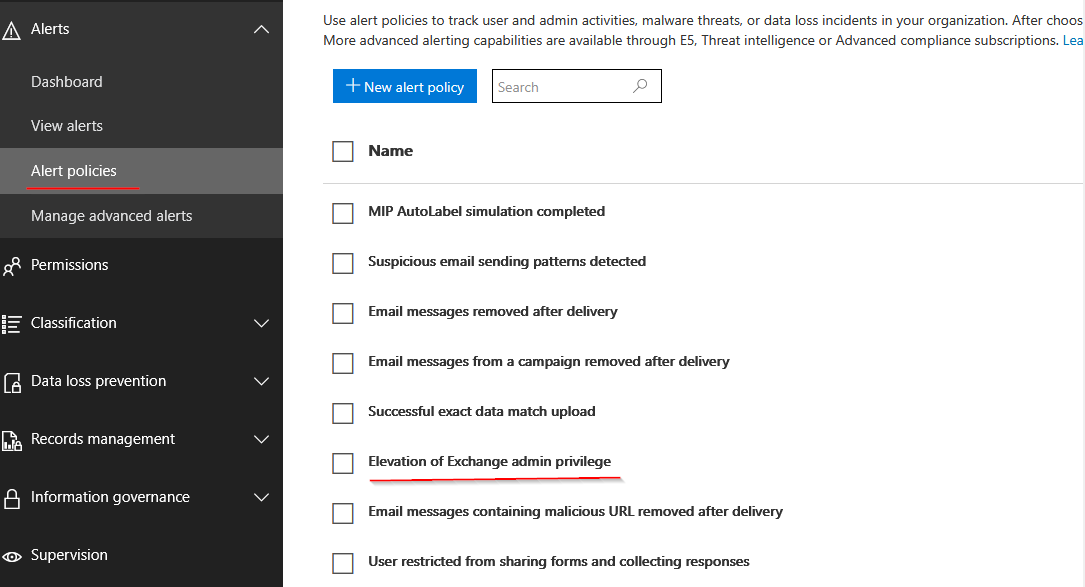
Since the answer is given in the documentation, the other options are incorrect.
Reference: To know more about alert policies, please refer to the link below: https://docs.microsoft.com/en-us/microsoft-365/compliance/alert-policies?view=o365-worldwide
Domain : Implement and manage identity and access
Q9 : You have a Microsoft 365 subscription and are planning to install AD Connect to support an Active Directory hybrid identity solution. Your company is using a 3rd party authentication solution that requires smartcards. You need to choose an authentication method for the Azure AD hybrid identity solution. What do you do?
Solution: You configure Pass-through authentication.
A. Yes
B. No
Correct Answer: B
Explanation:
Pass-through authentication is not compatible with 3rd MFA solutions or smartcards.
Pass-through authentication should be used when the password validation must be on-premise, as it relies on local Active Directory for authentication. It is set up by installing an agent on an on-premise server that allows Azure AD to validate local AD passwords and usernames.
Reference: To know more about Pass-through authentication, please refer to the link below: https://docs.microsoft.com/en-us/azure/active-directory/hybrid/how-to-connect-pta
Domain : Implement and manage identity and access
Q10 : You have a Microsoft 365 subscription and are planning to install AD Connect to support an Active Directory hybrid identity solution. Your company are using a 3rd party authentication solution that requires smartcards. You need to choose an authentication method for the Azure AD hybrid identity solution. What do you do?
Solution: You configure Password hash synchronization
A. Yes
B. No
Correct Answer: B
Explanation:
Password hash synchronization is not compatible with 3rd MFA solutions or smartcards.
Password hash synchronization synchronizes your AD DS user accounts with Microsoft 365 and manages your users on-premises. Hashes of user passwords are synchronized from your AD DS to Azure AD so that the users have the same password on-premises and in the cloud.
Reference: To know more about Password hash synchronization, please refer to the link below: https://docs.microsoft.com/en-us/azure/active-directory/hybrid/whatis-phs
Domain : Implement and manage identity and access
Q11 : You have a Microsoft 365 subscription and are planning to install AD Connect to support an Active Directory hybrid identity solution. Your company are using a 3rd party authentication solution that requires smartcards. You need to choose an authentication method for the Azure AD hybrid identity solution. What do you do?
Solution: You configure Federated authentication
A. Yes
B. No
Correct Answer: A
Explanation:
Federated authentication can support additional authentication requirements, such as smartcard-based authentication or a third-party multi-factor authentication
Federated authentication is most common for large organizations with complex authentication requirements. Users have the same password on-premise and in the cloud.
Reference: To know more about Federated authentication, please refer to the link below: https://docs.microsoft.com/en-us/azure/active-directory/hybrid/whatis-fed
Domain : Implement and manage identity and access
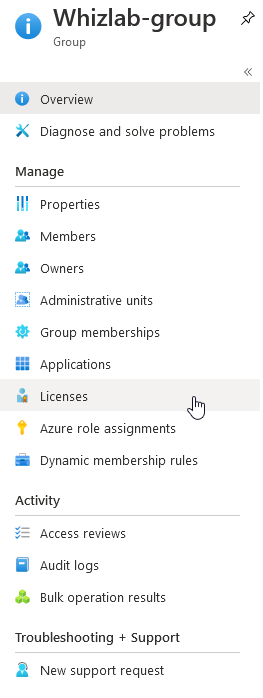
Q12 : You have a Microsoft 365 subscription with 30 E5 and 30 E3 available licenses. Your company has 3 departments: IT, Sales and Management. You need to make sure all users in the Management department will be assigned the E5 license automatically with the least amount of management on your end. What should you do?
A. In Azure Active Directory, create a security group with dynamic membership rules. Set the rule property to department and value to “Management”, and then assign the E5 license to the security group
B. Assign the license manually when creating the new users
C. Create an access review
D. Create a powershell script that assigns E5 license to Management-users and run it weekly
Correct Answer: A
Explanation:
Best approach here is to create a dynamic membership security rule that will automatically include all users in the Management-department.
By assigning the license to the security group, all users within the group will be licensed.

Option B is incorrect. This will not assign the licenses automatically and would be time-consuming.
Option C is incorrect. Access reviews are typically used to scope out user access and assignments. Not the way to go here.
Option D is incorrect. This will not assign the licenses automatically and is time-consuming.
Reference: To know more about azure AD dynamics groups, please refer to the link below: https://docs.microsoft.com/en-us/azure/active-directory/enterprise-users/groups-create-rule
Domain : Manage governance and compliance features in Microsoft 365
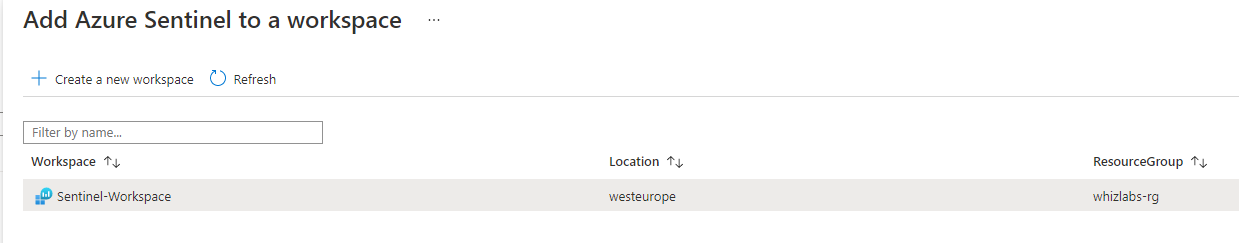
Q13 : You are a global administrator in a company with Microsoft 365 E5 licenses assigned to your users. The company is planning onboarding to Azure Sentinel as a solution to proactively detect and stop threats. You will be deploying the solution. What is the first thing you must do?
A. Create a new Log Analytics Workspace
B. Upgrade your license to Microsoft Defender for Office 365 plan 2
C. Create a conditional access policy
D. Within Azure Sentinel, connect a data source
Correct Answer: A
Explanation:
To enable Azure Sentinel, you must first create a Log Analytics Workspace. After it is created you will add Azure Sentinel to the new workspace:
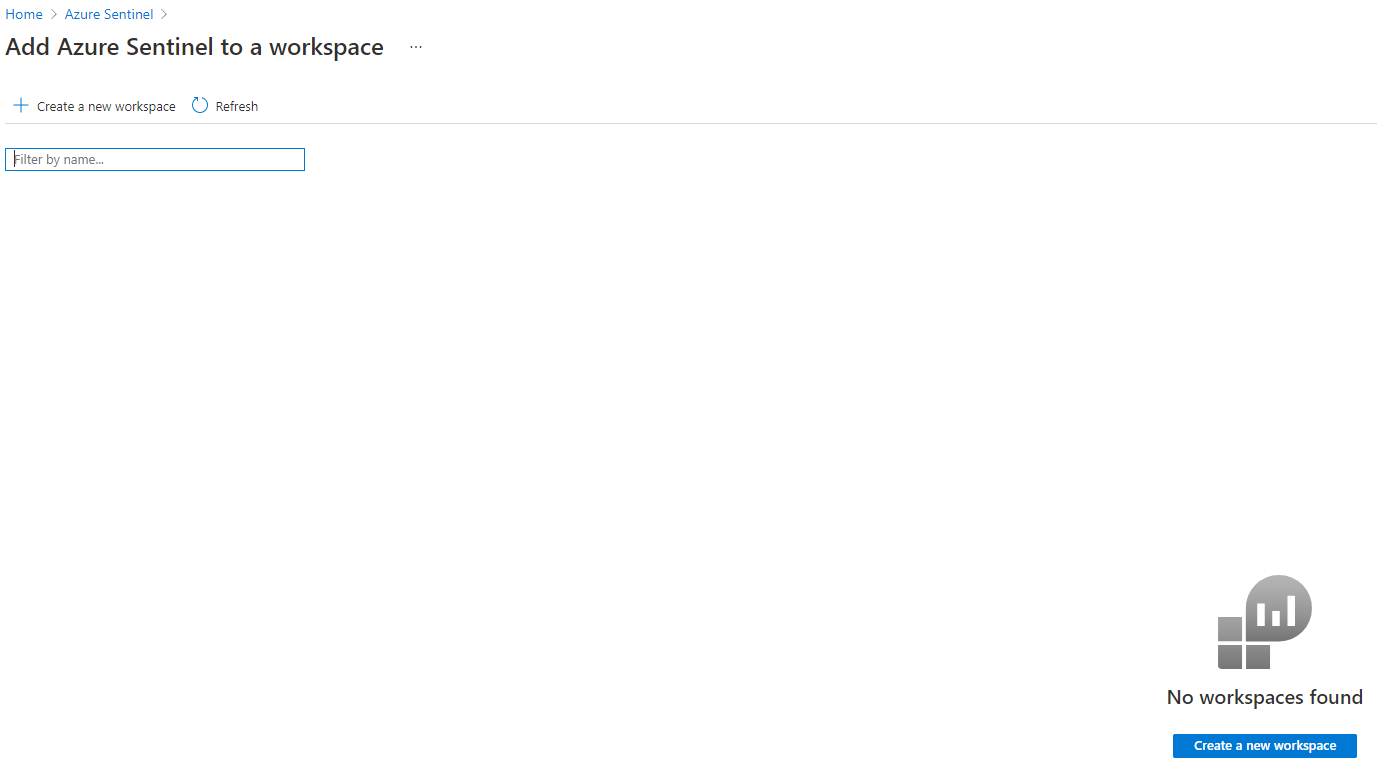
After these steps are completed you can start configuring your Sentinel solution by adding data sources.
Option B is incorrect. This is not a requirement to deploy Azure Sentinel.
Option C is incorrect. Creating a conditional access policy is not relevant in this scenario.
Option D is incorrect. You must first create a Log Analytics Workspace and the add Sentinel to the workspace.
Reference: To know more about onboarding to Azure Sentinel, please refer to the link below: https://docs.microsoft.com/en-us/azure/sentinel/quickstart-onboard
Domain : Implement and manage information protection
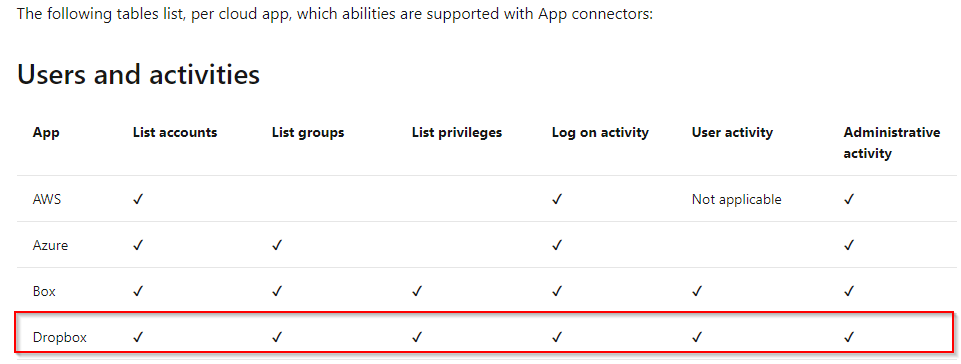
Q14 : You are the IT administrator in a company with a Microsoft 365 E5 subscription. Your users are using Dropbox daily, and you want to be able to view the user activity from your organization in Dropbox. What should you configure?
A. In Cloud App Security – App connectors – Add an app
B. In Azure AD – register an app
C. In Cloud App Security – Control – Templates – Create a policy
D. In Azure AD – Create an access package
Correct Answer: A
Explanation:
You can get visibility over the apps your users connect to by using Microsoft Cloud App Security.
You add an app by navigating to App connectors within Cloud App Security, and configuring steps to connect to the app. When the app is connected to gain visibility into the usage.
See Microsoft documentation:
Option B is incorrect. Registering an app in Azure AD is not relevant in this scenario.
Option C is incorrect. Creating policies within cloud app security allows you to create governance actions and set data loss prevention and file-sharing controls.
Option D is incorrect. Creating an access package in Azure AD is not relevant in this scenario.
Reference: To know more about cloud app security, please refer to the link below: Deploy Cloud App Security | Microsoft Docs
Domain : Manage governance and compliance features in Microsoft 365
Q15 : You are a global admin in a company with a Microsoft 365 subscription. In Microsoft 365 Compliance Center you have created a new Content Search, and now wish to export the result. What do you need first to export the findings?
A. a certificate
B. a shared access key
C. an export key
D. a password
Correct Answer: C
Explanation:
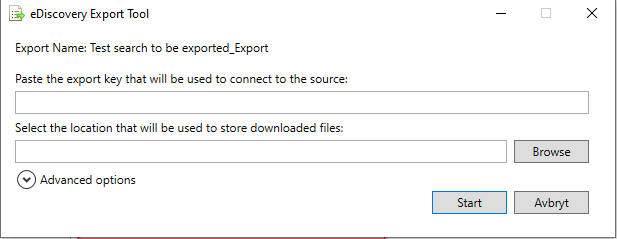
After you have created a content search and waited for it to finish, you can export the results (given you have the appropriate role permissions). However, you must first obtain the Export key which will be needed when you download the results:
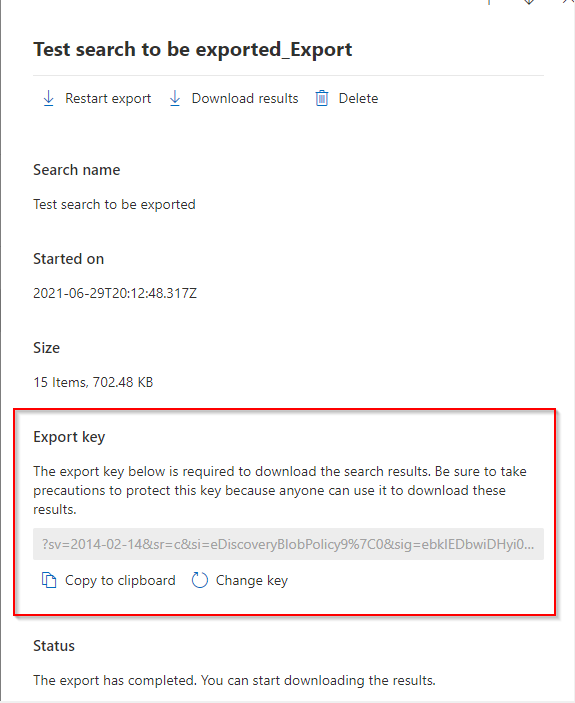
Reference: To know more about exporting content searches, please refer to the link below: https://docs.microsoft.com/en-us/microsoft-365/compliance/export-search-results?view=o365-worldwide
Domain : Manage governance and compliance features in Microsoft 365
Q16 : You are a global admin in a company with a Microsoft 365 subscription. In Microsoft 365 Compliance Center you have created a new Content Search, and you want your helpdesk to be able to export the result. How should you enable them to do this? You must use the principle of least privilege.
A. In Security & Compliance Center, add the users to the eDiscovery Manager role
B. In Office 365 admin center, add the users to the Helpdesk Administrator role
C. In Security & Compliance Center, add the users to the eDiscovery Administrator role
D. In Security & Compliance Center, add the users to the Compliance Administrator role
Correct Answer: A
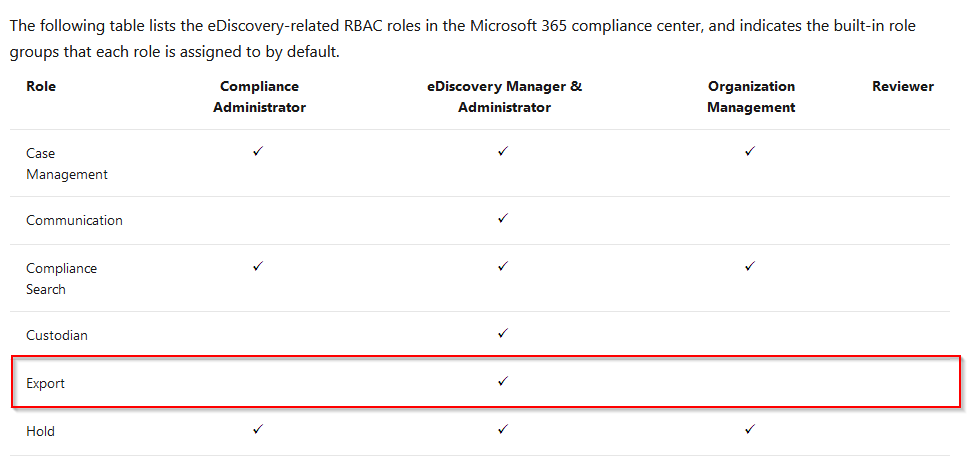
Explanation:
The least privileged role with permission to export content search results are the eDiscovery Manager role.
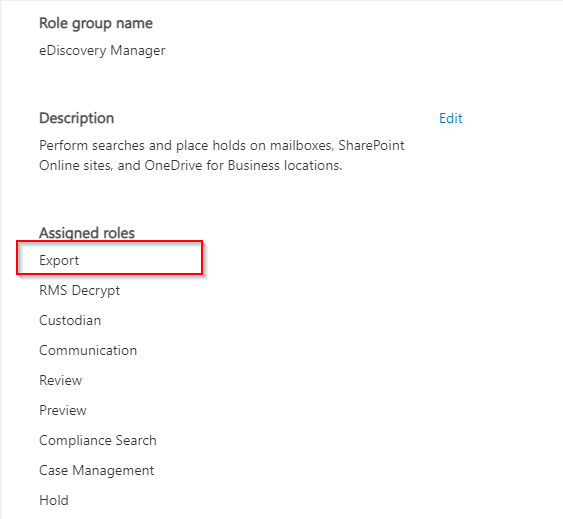
Option B is incorrect. This role will not permit you to export content search results.
Option C is incorrect. This role will allow you to export content search results, but it is not the least privileged alternative.
Option D is incorrect. This role will not permit you to export content search results.
Reference: To know more about content search permissions, please refer to the link below: https://docs.microsoft.com/en-us/microsoft-365/compliance/export-search-results?view=o365-worldwide
Domain : Manage governance and compliance features in Microsoft 365
Q17 : You are a global admin in a company with a Microsoft 365 subscription. Your users have their mailboxes in Exchange online. You have no archiving solution and wish to enable mailbox archiving within Office 365 for all users. What should you do first?
A. In Exchange Online admin center, select Migration -> Batch
B. In Exchange Online admin center, select Organization -> Sharing
C. In Security & Compliance Center, select Information governance -> Archive
D. In Security & Compliance Center, select Information governance -> Retention
Correct Answer: C
Explanation:
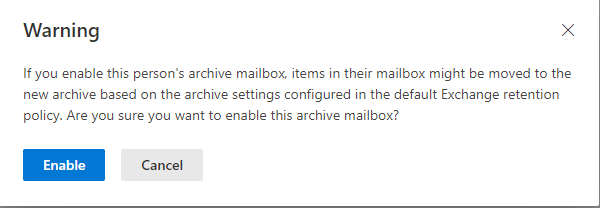
You can enable archive for your users by:
Navigate to Security & Compliance Center, select Information governance, select Archive:
Select all mailboxes by clicking on the first one in the list, holding down the Shift key, and then clicking the last one in the list.
In the details pane, under Bulk Edit, click Enable.
View the warning and click Enable to start the process.
Option A is incorrect. This is related to migration workloads from exchange on-premise to exchange online.
Option B is incorrect. This is related to sharing configurations between yours and other organizations.
Option D is incorrect. This is related to setting up retention policies to determine what items to keep and for how long.
Reference: To know more about setting up mailbox archiving, please refer to the link below: https://docs.microsoft.com/en-us/microsoft-365/compliance/set-up-an-archive-and-deletion-policy-for-mailboxes?view=o365-worldwide
Domain : Manage governance and compliance features in Microsoft 365
Q18 : You are a global admin in a company with a Microsoft 365 E5 subscription. You notice that some users have set up email forwarding out of your organization. In response to this you have enabled the “Creation of forwarding/redirect rule” policy and configured yourself as the recipient of the alerts. However, you find that the number of informational emails received due to the policy feels a bit like spamming and wish to enforce a daily notification limit to 10 emails. What should you configure?
A. In Microsoft 365 Compliance center – Policies – Alerts Policies, edit the built-in policy
B. In Microsoft 365 Compliance center – Alerts – Suppress an alert
C. In Microsoft 365 Compliance center – Alerts – Dismiss an alert
D. In Microsoft 365 Compliance center – Policies – Alerts Policies, create a new policy
Correct Answer: A
Explanation:
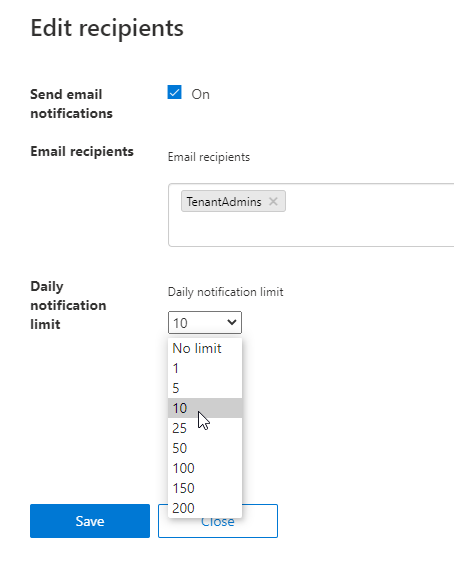
You should edit the built-in policy and change the daily notification limit to 10:
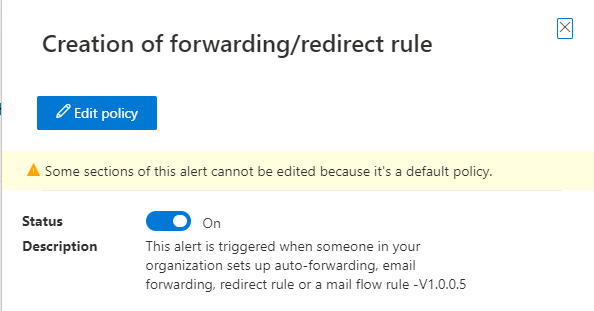
Option B is incorrect. This will only suppress an existing alert.
Option C is incorrect. This will only dismiss an existing alert.
Option D is incorrect. There is no need to create a new policy, you should edit the existing built-in policy.
Reference: To know more about setting up alert policies, please refer to the link below: https://docs.microsoft.com/en-us/microsoft-365/compliance/alert-policies?view=o365-worldwide
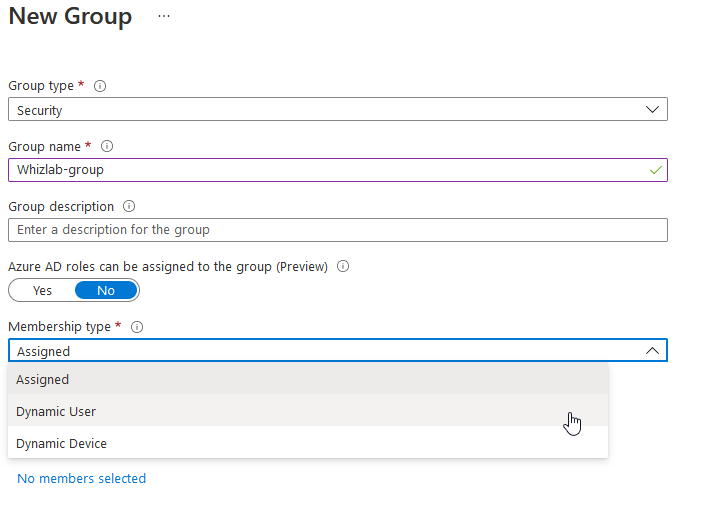
Domain : Implement and manage identity and access
Q19 : You have a Microsoft 365 subscription and Azure AD on the Premium P1 tier. You are planning license allocation and want to create a group that will automatically add all users from the Sales-department. What kind of group in Azure Active Directory should you create?
A. Group type: Security, Membership type: Assigned
B. Group type: Security, Membership type: Dynamic Device
C. Group type: Security, Membership type: Dynamic User
D. Group type: Microsoft 365, Membership type: Assigned
Correct Answer: C
Explanation:
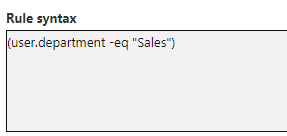
You should create a security group with the dynamic user membership type, and add the dynamics query:
(user.department -eq “Sales”)
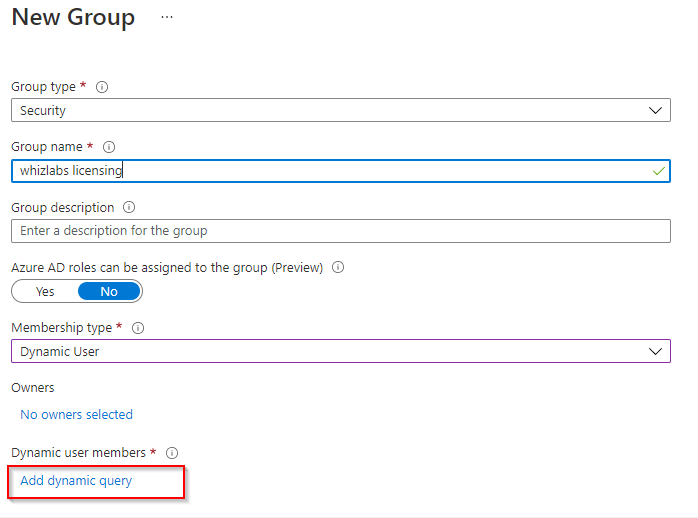
Option A is incorrect. Assigned membership type will not automatically assign your licenses based on a query.
Option B is incorrect. We are using the attribute “department” which is associated with the Azure AD user, not device.
Option D is incorrect. For assigning licenses we should use a Security group, not Microsoft 365. Also the membership type is Assigned, which will not let us create a query to assign licenses based on department information.
Reference: To know more about Azure AD dynamics groups, please refer to the link below: https://docs.microsoft.com/en-us/azure/active-directory/enterprise-users/groups-dynamic-membership
Domain : Implement and manage identity and access
Q20 : You are the IT administrator of a company with a Microsoft 365 subscription. You have just enabled self-service password reset for all your users. What will be the user experience the next time your users sign in to your tenant?
A. There is no user impact after enabling self-service password reset
B. Your users will be prompted to enter additional contact information
C. Your users will be redirected to Microsoft Store for Business, where they must download the authenticator app
D. Your users must update their passwords
Correct Answer: B
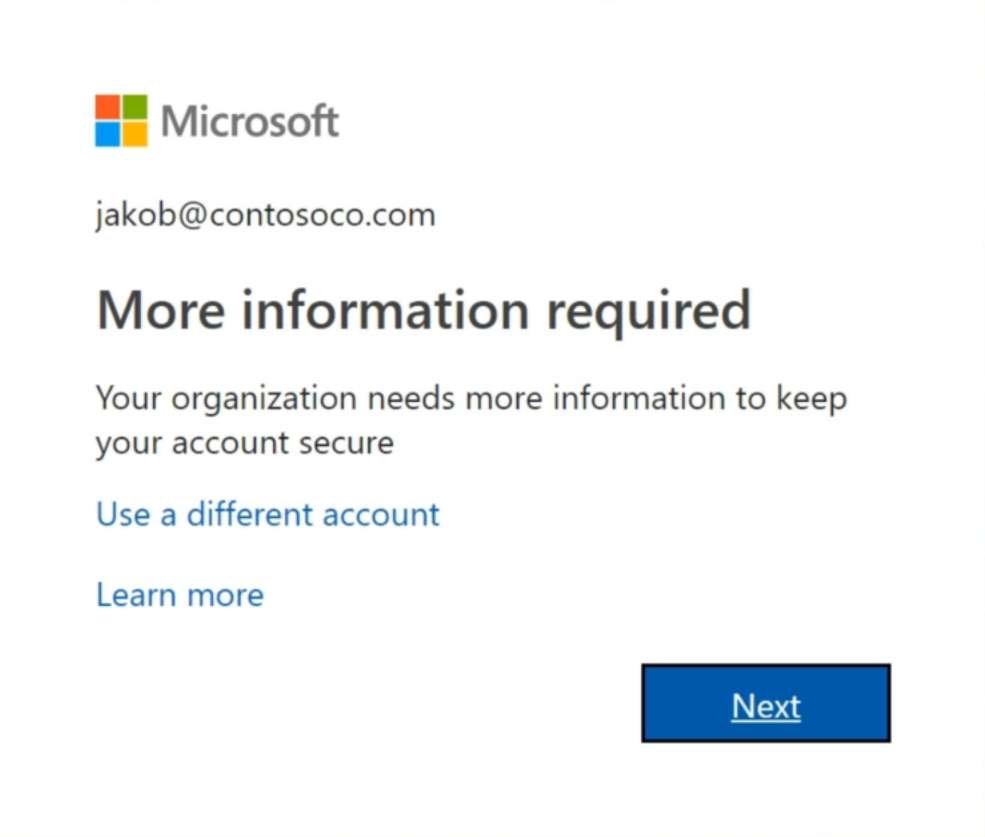
Explanation:
Your users will get a prompt stating “More information required”, where they need to enter additional contact information that is needed to reset their password in the future.
Option A is incorrect. There is a user impact after enabling the service.
Option C is incorrect. This will not happen, and the authenticator app is for mobile devices.
Option D is incorrect.
Your users will not be asked to update their passwords.
Reference: To know more about enabling password reset, please refer to the link below: https://docs.microsoft.com/en-us/microsoft-365/admin/add-users/let-users-reset-passwords?view=o365-worldwide
Domain : Implement and manage identity and access
Q21 : You have a Microsoft 365 subscription, and you are responsible for securing your Office 365 tenant. You want to set your users passwords to expire after 90 days.
How should you configure this?
A. In Microsoft 365 admin center-> Setting -> Org settings
B. In Azure Active Directory – Password reset – Customization
C. In Azure Active Directory – Security – Security Center
D. In cloud shell – Get-AzureADUser -All $true | Set-AzureADUser -PasswordPolicies DisablePasswordExpiration
Correct Answer: A
Explanation:
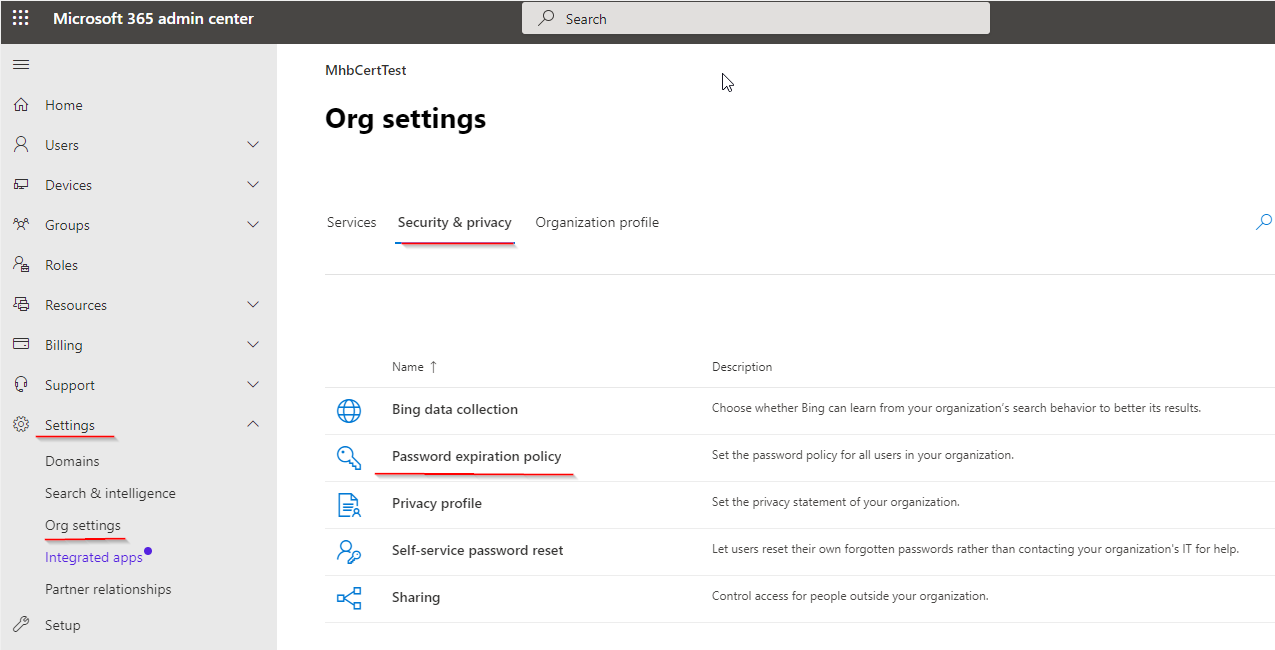
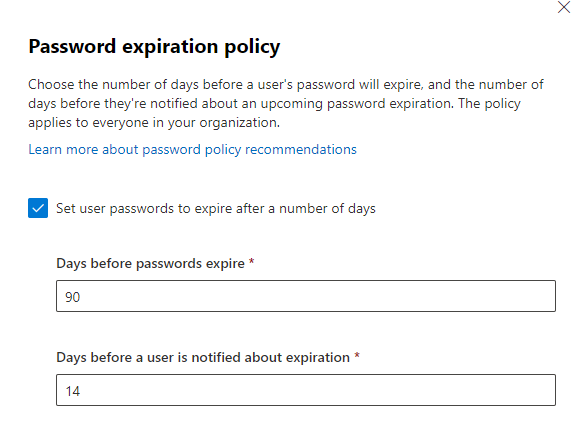
You should navigate to Microsoft 365 admin center, Settings, Org settings, Security & Privacy and select Password expiration policy
Set the “Days before passwords expire” to 90 days.
Option B is incorrect. This is where you customize a helpdesk link
Option C is incorrect. Azure security center is a hub for administering security status and threat protection.
Option D is incorrect. This command removed password expiration.
Reference: To know more about configuring org wide password policy, please refer to the link below: https://docs.microsoft.com/en-us/microsoft-365/admin/manage/set-password-expiration-policy?view=o365-worldwide
Domain : Implement and manage threat protection
Q22 : You have a Microsoft 365 subscription and Microsoft 365 E5 licenses assigned to your users. You are using Microsoft Defender for Office 365, and you configure a safe attachment policy for your Sales department. You want the emails containing malicious attachments to be delivered without the attachment. How should you configure the policy?
A. Block
B. Replace
C. Dynamic Delivery
D. Monitor
Correct Answer: B
Explanation:
You should configure the policy with the Replace-control. When enabled, detected malware attachments will be removed, but the message will be delivered (without the attachment).
Option A is incorrect. This control prevents messages with detected malware attachments from being delivered.
Option C is incorrect. This control replaces the attachment with a placeholder until the Safe attachment scanning is complete. If found to be safe, the attachment is then released to the user.
Option D is incorrect. This control only tracks what happens with detected malware.
Reference: To know more about Safe attachment configurations, please refer to the link below: https://docs.microsoft.com/en-us/microsoft-365/security/office-365-security/safe-attachments?view=o365-worldwide
Domain : Implement and manage information protection
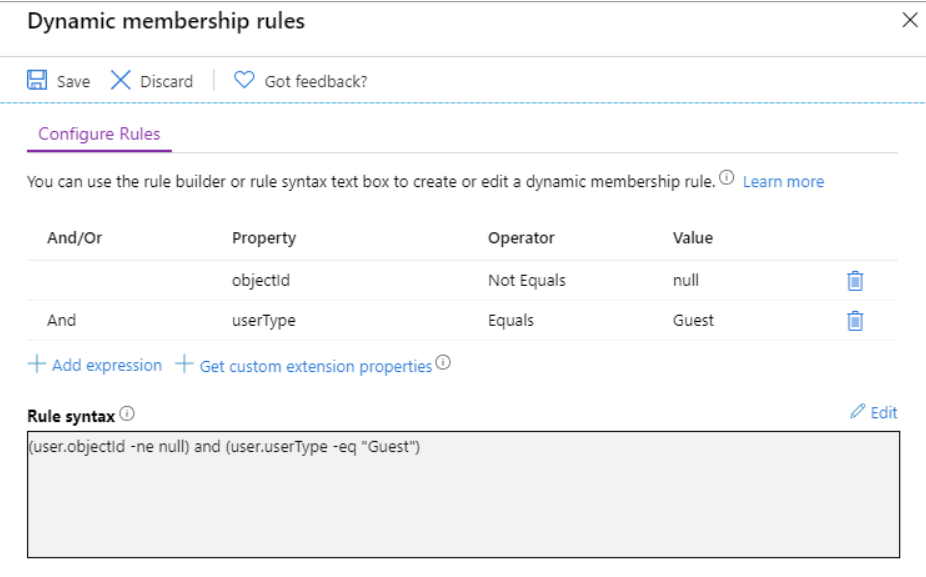
Q23 : You have a Microsoft 365 subscription. Your organization is frequently collaborating with external users from different companies. You have created a dynamic group in Azure AD to automatically add new and old guest users.
How should you configure the rule syntax?
A. (user.objectId -ne null) and (user.userType -eq “Member”)
B. (user.objectId -e external) and (user.userType -eq “Guest”)
C. (user.objectId -e external) and (user.userType -eq “Member”)
D. (user.objectId -ne null) and (user.userType -eq “Guest”)
Correct Answer: D
Explanation:
The correct expression is (user.objectId -ne null) and (user.userType -eq “Guest”) – you are adding all users that have an existing user object ID with the user type “guest”.
Option A is incorrect. This is not a valid expression
Option B is incorrect. This is not a valid expression.
Option C is incorrect. This expression will add users with the user type Member – internal tenant users.
Reference: To know more about grouping guest users, please refer to the link below: https://docs.microsoft.com/en-us/azure/active-directory/external-identities/use-dynamic-groups
Domain : Manage governance and compliance features in Microsoft 365
Q24 : You are a global admin in a company with a Microsoft 365 subscription and Microsoft 365 E5 licenses assigned to your users. You have set up several retention policies and labels. Due to rules defined by regulatory bodies you need to make sure one specific policy cannot be turned off, deleted or made less restrictive.
What should you configure?
A. Azure Resource Group – Locks
B. Litigation Hold
C. Azure DevOps release pipeline
D. Preservation Locks
Correct Answer: D
Explanation:
You should configure a preservation lock on the policy that must be protected. This will ensure that it cannot be changed, deleted or turned off.
You can enable Preservation Lock by connecting to Security & Compliance Powershell and use the Set-RetentionCompliancePolicy cmdlet with the name of the policy:
Set-RetentionCompliancePolicy -Identity “<Name of Policy>” –RestrictiveRetention $true
Option A is incorrect. This feature prevents deletion of resource groups.
Option B is incorrect. This service places a mailbox on hold for a specified timeframe.
Option C is incorrect. Azure DevOps release pipelines are used for releasing a built artifact to for instance Azure.
Reference: To know more about preservation locks, please refer to the link below: Use Preservation Lock to restrict changes to retention policies and retention label policies – Microsoft 365 Compliance | Microsoft Docs
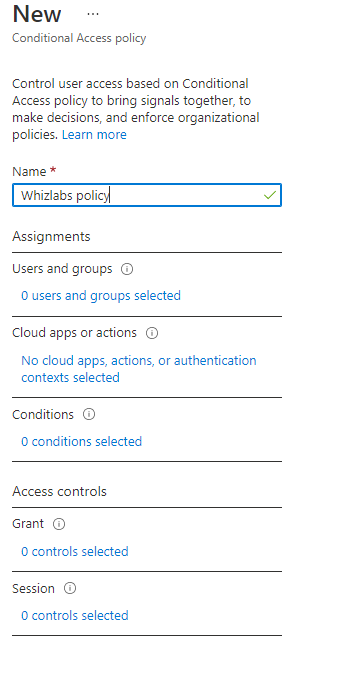
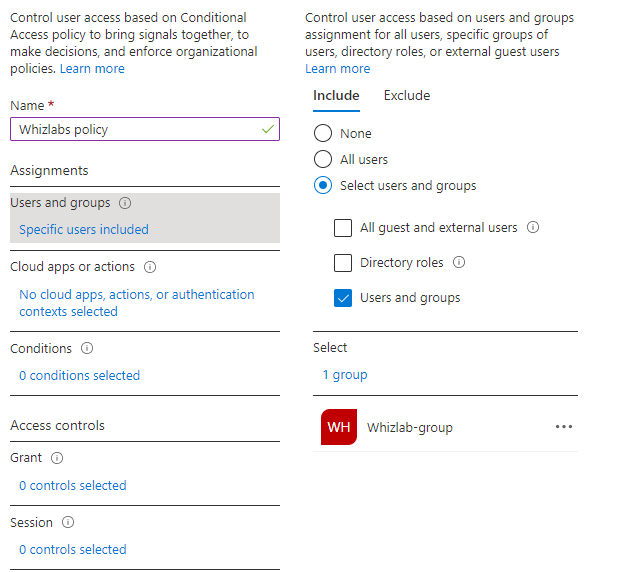
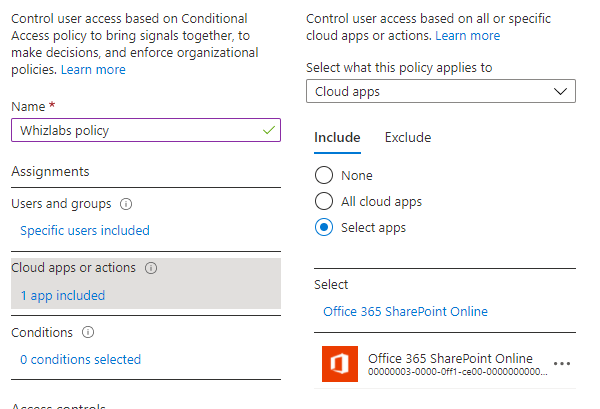
Domain : Implement and manage identity and access
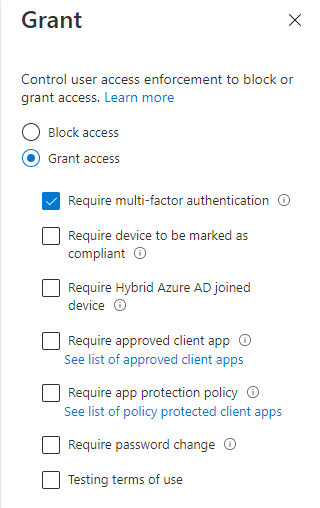
Q25 : You are creating an Azure AD conditional access policy. You want to enforce multi-factor authentication for a selected set of users when logging on to sharepoint online.
Which controls should you configure?
A. Users and groups
B. Cloud apps or actions
C. Conditions
D. Grant
E. Session
Correct Answers: A, B and D
Explanation:
Under Users and groups, you target the selected users:
Under Cloud apps or actions, you select Sharepoint online:
Under Grant you select the action that will be enforced, in this case granting access after MFA authentication:
Option C is incorrect. Conditions control user access based on signals from conditions like risk, device platform, location, client apps, or device state.
Option E is incorrect. Sessions Control user access based on session controls to enable limited experiences within specific cloud applications.
Reference: To know more about password enabling MFA in Conditional access, please refer to the link below: https://docs.microsoft.com/en-us/azure/active-directory/authentication/tutorial-enable-azure-mfa
Summary:
Hope you have learned the Microsoft 365 security certification questions. If you are looking for Microsoft 365 Security Administration training, then this blog post can help you in building confidence for passing the actual exam. As a part of your MS-500 preparation, you should also give a try on MS-500 practice tests which have similar questions related to the real exam and a detailed study guide. Keep learning !
- Top 25 DevSecOps Interview Question and Answers for 2024 - March 1, 2023
- How to prepare for VMware Certified Technical Associate [VCTA-DCV] Certification? - February 14, 2023
- Top 20 Cloud Influencers in 2024 - January 31, 2023
- 25 Free Question on SC-100: Microsoft Cybersecurity Architect - January 27, 2023
- Preparation Guide on MS-101: Microsoft 365 Mobility and Security - December 26, 2022
- Exam tips to prepare for Certified Kubernetes Administrator: CKA Exam - November 24, 2022
- Why do you need to upskill your teams with the Azure AI fundamentals? - October 11, 2022
- The best employee retention strategy for IT industries – UPSKILLING - September 26, 2022