Chef vs Puppet vs Ansible comparison is important to identify the ideal configuration management tool for specific projects. Let’s dive deep to understand the differences between Chef, Puppet, and Ansible!
The importance of DevOps in the modern IT landscape is unquestionable. DevOps provides various components that should work together to address the shared objectives of a team. One of the most significant elements in the DevOps methodology is configuration management. Therefore, it is common to observe debates on the effectiveness of different configuration tools such as Chef, Puppet, and Ansible.
Configuration management involves the use of configuration items that are configurable and essential for the success of DevOps projects. Configuration items can include servers, source codes, tools, binaries, and property files. The different processes involved in configuration management include configuration identification, configuration audit, and configuration control.
The primary objective of DevOps is the development of software quickly, and this is possible only through appropriate planning and organization. Detailed configuration management could deliver substantial power for achieving DevOps objectives. If you are a DevOps professional, you also need to understand its comparison with Terraform vs Ansible, and Chef vs Ansible which is commonly asked.
Preparing to become a certified DevOps professional? Check our DevOps Certifications Training Courses now!
Chef vs Puppet vs Ansible – A Complete Comparison
The need for Ansible, Chef and Puppet comparison is evident in the need to identify the ideal configuration management tool for specific projects. All three tools are simple in terms of usability. The three configuration management tools also provide powerful capabilities for the automation of complex multi-tier IT application environments. The following discussion would aim at exploring the differences between Ansible, Chef, and Puppet on the basis of different factors. The evaluation of insights from this discussion can help in comparing the pros and cons of the three tools.
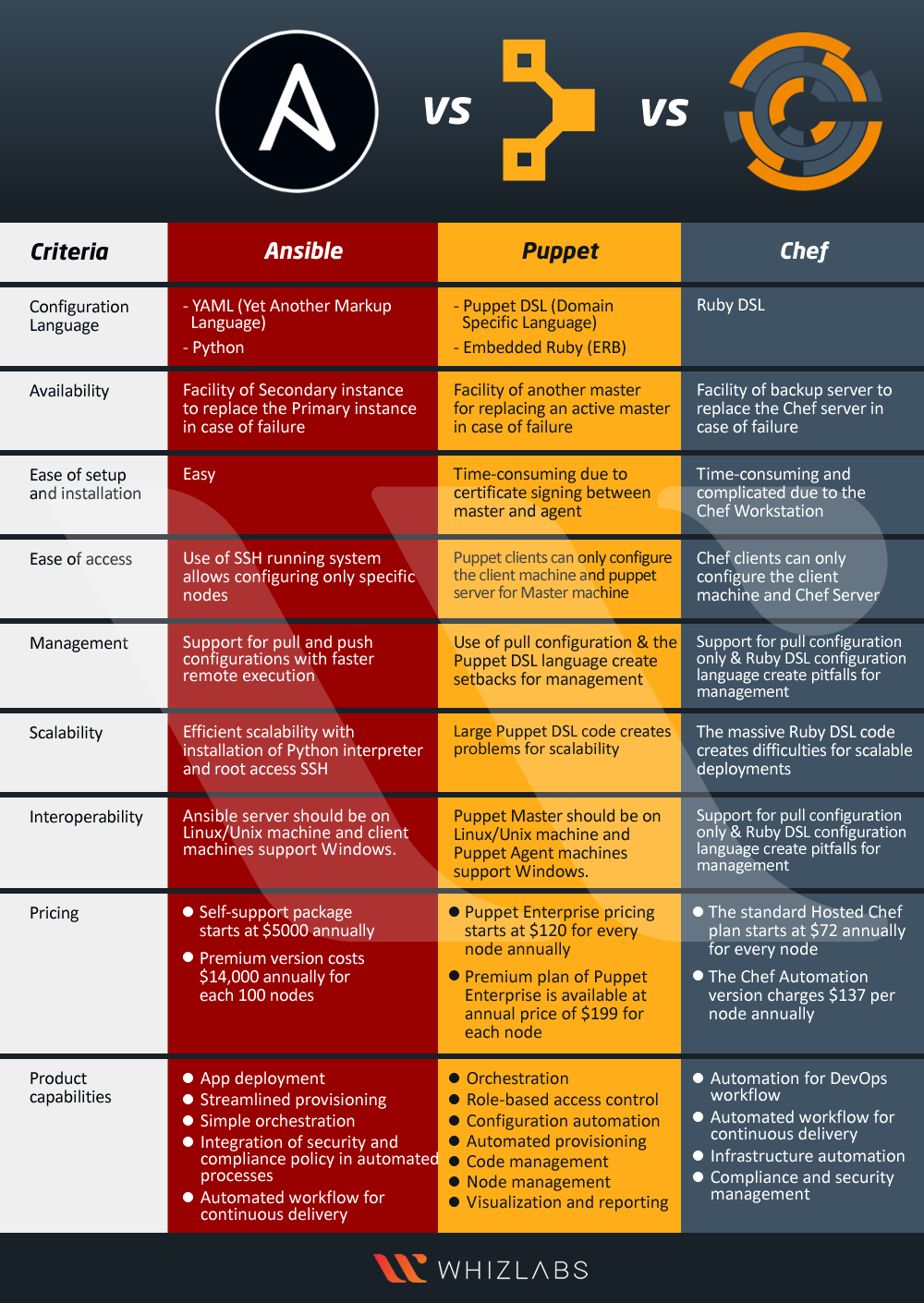
1. Configuration Language
The first point of comparison in the Chef vs Puppet vs ansible debate is the support for programming languages. This factor is one of the most important factors for determining the usability of a configuration management tool.
- Ansible offers support for Python as it is written on Python. In addition, Ansible also provides support for YAML command scripts. Python is commonly in-built in major Linux and Unix deployments. Furthermore, Python is human-readable and presents a credible advantage for Ansible in this Ansible vs Chef vs puppet comparison. Ansible is ideal for system administrators and has a very simple learning curve.
- Puppet configuration management tool has Ruby as its foundation language, thereby implying support for it. Puppet uses the Puppet DSL language that is difficult to learn. In addition, Puppet provides support only for Embedded Ruby (ERB) and Domain Specific Language (DSL). The configuration language of Puppet is suitable for system administrators.
- Chef provides support for Ruby DSL along with the facility of crucial prototype programming. Therefore, users can find a difficult learning curve with Chef. It is ideal for developers.
2. Availability
Availability is also a prominent requirement in DevOps that serves as the ideal foundation for ansible chef puppet comparison. All three tools claim higher availability with the facility of multiple servers and instances. The effectiveness of availability in a configuration management tool is evident in the facility of a backup server or an alternative master in the event of the failure of the main master or server.
- Ansible runs with a single active node. The single active node, known as the Primary instance, has a secondary instance for replacing it in the event of failure.
- Puppet follows a multi-master architecture. As a result, in the event of the failure of the active master, another master can replace it.
- Chef also provides assurance of higher availability through the facility of a backup server. The backup server can replace the primary server or the chef-server in the event of any failure on the primary server.
Enroll Now: Puppet 206 Online Training Course
3. Ease of Setup
Setting up a configuration management tool is also a prominent differentiator in the Chef vs Puppet vs Ansible comparison. A brief overview of the installation processes for each configuration management tool can provide reliable insights on the ease of setup for each tool.
- Ansible has the master running on the server machine without any agents running on the client machine. The architecture of Ansible is one of its promising highlights among chef puppet ansible difference pointers. Ansible utilizes SSH connection for logging in to client systems. The SSH connection is also available for connecting to nodes that the user wants to configure. Furthermore, the client machine VM (virtual machine) does not require any form of special setup. On an overall basis, setting up Ansible is nothing less than a walk in the park!
- Puppet follows a master-agent or master-slave architecture. In the case of Puppet’s architecture, the master machine serves as the platform for running the Puppet server. The client machines provide the platforms for running Puppet clients as agents. In addition, the requirement of signing a certificate between the master machine and the agent adds complexity. Therefore, Puppet does not ensure flexible ease of setup like Ansible. Apart from the difficult initial setup process, Puppet is also difficult when it comes to identifying errors during installation.
- Chef follows the cue of Puppet in this section of the Chef vs Puppet vs ansible debate. How? The master-slave architecture of Chef implies running the Chef server on the master machine and running the Chef clients as agents on different client machines. Apart from these similarities with Puppet, Chef also has an additional component in its architecture, the workstation. The workstation holds all the configurations. The workstation is the ideal place for testing the configurations before pushing them to the central chef server. As a result, the concerns of setup with Chef are primarily evident in higher time consumption. Furthermore, the installation of Chef requires effective programming expertise.
Preparing for an Ansible certification? Read our preparation guide for the Ansible certification and bring your career to the next level.
4. Ease of Access
The exact focus in this section for comparing Chef vs Puppet vs Ansible is not on security. A broader idea of the functionality of each configuration management tool and the access privileges can also establish a strong differentiator for these tools. The most important aspect of the chef puppet ansible difference based on ease of access is the architecture of the tools.
- The operating framework of Ansible depends on a single active node. Therefore, Ansible utilizes the SSH running system for the configuration of the nodes according to user preferences.
- Puppet stands out in the Ansible vs Chef vs puppet debate in this case due to a master-slave architecture. The operating framework follows a master-slave architecture. So, only the clients on Puppet could have the privileges of configuring the puppet server for the Master machine and client machine.
- Chef also relies on the master-slave architecture, thereby implying the facility of access privileges to Chef clients only. Chef clients can only configure the master machine and client machine.
Read Now: Ansible Best Practices
5. Management
Another prominent differentiator in the Chef vs Puppet vs ansible comparison is the flexibility of management. The most important aspect to understand the differences between Ansible, Puppet, and Chef in terms of management is the type of configuration in each tool. There are two types of configurations, such as push configuration and pull configuration. Ansible follows push configuration while Puppet and Chef follow the pull configurations. In the case of pull configuration, the slave nodes would pull all configurations from a central server without commands. On the other hand, the push configuration involves pushing configurations in the central server to the nodes through specific commands. Let us look at the ease of configuration management with the three different tools as follows.
- Ansible supports considerable ease of learning for the management of configurations due to YAML as the foundation language. YAML (Yet Another Markup Language) is closely similar to English and is human-readable. The server can help in pushing configurations to all the nodes. The applications of Ansible are clearly suitable for real-time execution along with the facility of faster remote execution. The difference between Chef, Puppet, and Ansible, in this case, turns towards the favor of Ansible. Ansible can use pull as well as push processes for distributing configuration to the nodes. As a result, all servers could communicate with each other alongside improving the speed of communication.
- Puppet follows the pull configuration type and exhibits difficulty in management due to the Puppet DSL language. The clients have to pull configurations from the server. Puppet does not provide immediate remote execution. Therefore, it is applicable specifically for system administrators.
- Chef also follows a domain-specific language i.e., Ruby DSL. In addition, it does not have push configuration processes. A chef tends to show similarities with Puppet in this section of Chef vs Puppet vs ansible comparison. Clients have to pull configurations from the server, and the addition of complicated steps reduces the effectiveness of communication in Chef.
Preparing for Ansible interview? Here’re the top 20 Ansible interview questions that will make you ready for the interview.
6. Scalability
One of the most important requirements of enterprises opting for configuration tools is scalability. Therefore, it is an important criterion for comparing Chef vs Puppet vs Ansible. However, evaluating the difference between Chef, Puppet, and Ansible on the basis of scalability is an ambiguous process. All three configuration management tools are ideal for the DevOps landscape, thereby implying the in-built functionalities for scalability. The tools are capable of managing large infrastructures while bearing the lion’s share of the burden in scaling configurations. However, there are certain factors which could help in drawing out fine comparisons between Chef, Puppet, and Ansible in terms of scalability.
- Ansible tends to be a reliable alternative for accomplishing scalable deployments. Ansible users can achieve a proper workflow through the installation of Python interpreter and root access SSH. This is the only prerequisite to ensure faster scalability on Ansible. These measures ensure that the scaled environment does not slow down due to discrepancies in communication with SSH.
- Puppet does not score good points when it comes to scalability in a chef vs Puppet vs ansible comparison. The primary reason for the lack of support for scalability in Puppet is its configuration language. The DSL code could be extremely large, thereby leading to complicated issues at higher scaling.
- Chef also depicts similar problems for scalability like Puppet. The Ruby DSL code is also large and can lead to various issues during deployment at a larger scale.
7. Interoperability
The outcomes of Chef vs Puppet vs ansible comparison in terms of interoperability shows glaring similarities. For starters, the master or main server (control machine) should be on Linux/Unix systems. On the other hand, the slaves or nodes that you have to configure in the three configuration tools support Windows. Let us take a look at the interoperability of each tool as follows.
- Ansible provides the benefit of interoperability by supporting Windows machines for the clients. However, the Ansible server should be on a Linux or Unix machine.
- The aspect of interoperability in Puppet is evident in the working of the Puppet Master only on Linux or Unix machines. The Puppet Agent or clients could also work on Windows machines.
- In the case of Chef, the Chef Server could work only on Linux or Unix machines. On the other hand, the Workstation and Chef Client could work on Windows machines also. Therefore, Chef is also capable of depicting similar interoperability as other players in the Chef vs Puppet vs ansible comparison.
Also Check: Top 25 Chef Interview Questions and Answers
8. Pricing
Pricing is a formidable differentiator in selecting the winner in a chef vs. Puppet vs. ansible comparison. Why? Flexible pricing is one of the prominent factors that drive the adoption of configuration management tools or, generally, any new technology. A closer look at the pricing schema of the three popular configuration management tools can also establish another helpful difference.
- In the case of Ansible, the Self-Support package starts at an annual price of $5000. The basic pricing of the Ansible Tower for standard IT operations is $10,000 annually, up to 100 nodes. The annual pricing for the Premium version of Ansible ranges up to $14,000 for every 100 nodes.
- The standard pricing in the case of Puppet Enterprise starts from $120 for every node annually. The interesting thing is that Puppet Enterprise is available for free up to 10 nodes. The Premium plan of Puppet Enterprise comes at $199 annually for each node.
- The most interesting aspect about Chef in this section of Chef vs Puppet vs ansible comparison is the facility of a free version. Users could start off with their configuration management needs through the free version of Chef. The standard annual pricing for every node in the standard Hosted Chef plan is $72. Most important of all, the Chef Automate version can provide exceptional configuration management facilities at an annual price of $137 per node.
9. Product Capabilities
Another notable aspect that is one of the top priorities while choosing a configuration management tool refers to product capabilities. The most reasonable approach to finalize the winner in Chef vs. Puppet vs. ansible debate is the review of product capabilities. A review of the product capabilities of each tool can offer a streamlined impression of their configuration management functionality.
- Ansible products offer simpler orchestration with easier workflows alongside streamlined provisioning. Apart from configuration management, Ansible can also offer the benefits of the automated workflow to ensure continuous delivery. In addition, Ansible product capabilities also include app deployment. Another important capability evidently visible in Ansible is the integration of security and compliance policy into automated processes.
- With the help of Puppet Enterprise product, users could gain orchestration capabilities with Puppet. The other capabilities with Puppet include automated provisioning, code management, and node management. The most important capability of Puppet Enterprise is evident in configuration automation. Most important of all, Puppet Enterprise provides assurance of security through role-based access control. In addition, users could also find the facility of simple visualization and reporting with Puppet, thereby ensuring higher transparency.
- The product capabilities of Chef exhibit certain similarities with that of Ansible and Puppet, albeit with certain stark differences. For example, you can find the facility of automated workflow for continuous delivery like Ansible and infrastructure automation feature like Puppet. Apart from these features, Chef offers reliable functionality of compliance and security management alongside automation for DevOps workflow.
You can find an overview of the differences between Ansible, Puppet, and Chef here –
Preparing for a puppet interview? Go through these top puppet interview questions and answers and get ready to ace the interview.
Conclusion
Every platform in the chef vs. puppet vs. ansible battle has a different approach towards automation and configuration management. The key inference from this discussion is that you cannot find a one-size-fits-all configuration management tool. Therefore, a comparative review of the three popular configuration management tools can offer credible advantages in the selection process.
Each configuration management tool is ideal for specific user segments in the same target markets. Therefore, teams should map some distinct requirements surrounding their workflows while investing in configuration management solutions. As a result, the teams could ensure a reliable improvement in productivity and ROI. The important factors that can help in making a better decision about a configuration management tool include the architecture. Other factors include usability, product features, support, and other relevant technical and business factors.
If you are a DevOps professional and want to validate your skills, it’s the right time to go for a DevOps certification. Check out our DevOps certification training courses and prepare yourself to become a certified DevOps professional.
- Top 10 Highest Paying Cloud Certifications in 2024 - March 1, 2023
- 12 AWS Certifications – Which One Should I Choose? - February 22, 2023
- 11 Kubernetes Security Best Practices you should follow in 2024 - May 30, 2022
- How to run Kubernetes on AWS – A detailed Guide! - May 30, 2022
- Free questions on CompTIA Network+ (N10-008) Certification Exam - April 13, 2022
- 30 Free Questions on Microsoft Azure AI Fundamentals (AI-900) - March 25, 2022
- How to Integrate Jenkins with GitHub? - March 22, 2022
- How to Create CI/CD Pipeline Inside Jenkins ? - March 22, 2022