Preparing for AWS Certified Security Specialty exam? Logging and Monitoring is an important domain in the exam blueprint with 20% weightage. So, to help you in your AWS Certified Specialty exam preparation, here we cover the the topic – How to Use a Central CloudTrail S3 Bucket for Multiple AWS Accounts that addresses the “Logging and Monitoring” domain as highlighted in the AWS Certified Security Specialty Exam Guide.
Let’s understand the problem statement first and then we’ll move to the solution.
Problem Statement
Nowadays, it is not uncommon for companies to have multiple AWS accounts. They could have separate accounts for different environments as shown below:
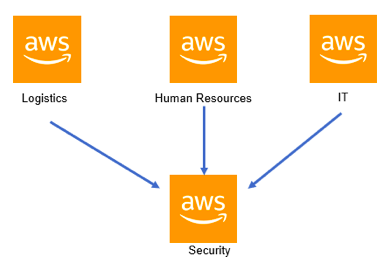
Or maybe have different accounts for different business units as shown below:
A very important aspect which is undertaken by organizations is to use CloudTrail to monitor all API calls. Some of the benefits of using CloudTrail are:
- You can monitor all the activity occurring in your AWS account
- It gives the security department to see if any malicious activity is occurring via unwarranted API calls
- Ability to stream the API calls to CloudWatch logs or S3 buckets for further analysis
But with the advent of so many accounts, using CloudTrail and multiple S3 buckets across so many accounts is normally not an ideal solution. What’s the most efficient solution to this problem then?
To Use a Central CloudTrail S3 Bucket for Multiple AWS Accounts, is the most-effective solution. Let’s dive deep to understand it.
Solution: Using Central CloudTrail S3 Bucket for Multiple AWS Accounts
Companies now adopt having a central Security account and stream all the CloudTrail logs into one account as shown below:
So let’s look at how you can implement central logging
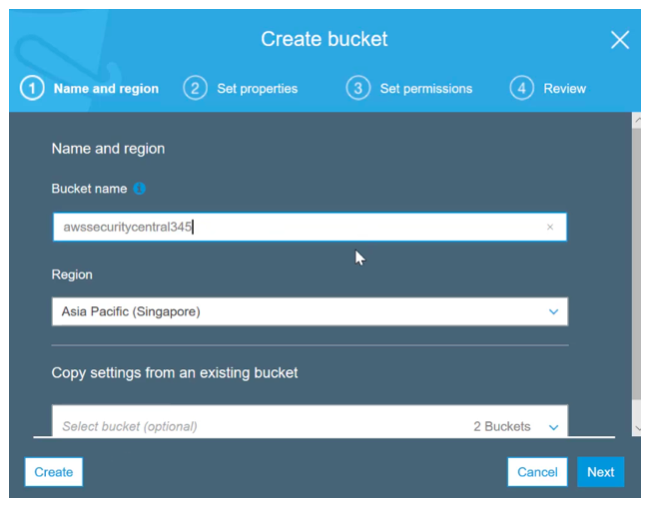
Step 1) Let’s assume that your central account is called cloud-production
In S3 , first create a bucket that will hold all of the CloudTrail log files
Also Read: How to Setup and Use Amazon S3?
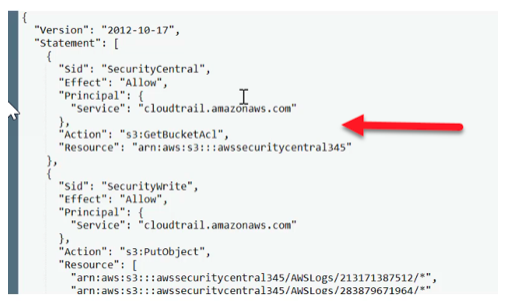
Step 2) Go to the bucket and add a bucket policy
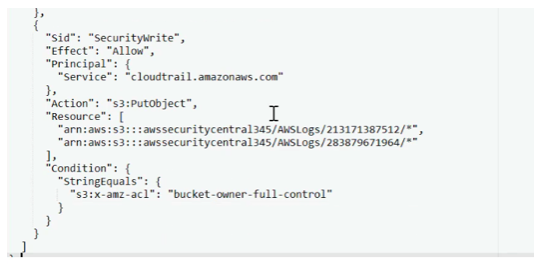
- In the bucket policy first add a policy statement to allow CloudTrail to have the permission to get the bucket ACL
- Next, we need to add the permissions for the accounts to have permissions to add objects to the bucket.
Here one account 283879671964 is the account number of the production or security account
And the other account 213171387512 is the account number of another account called cloud-staging. In the next step we are going to configure the cloud-staging account to use this bucket for logging purposes.
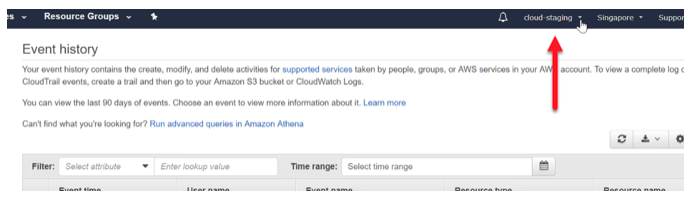
Step 3) Now log into the other account as shown below. Let’s refer this as the cloud-staging account
Go to the CloudTrail service
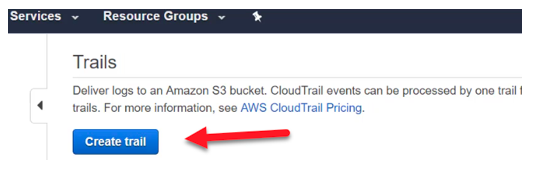
Step 4) Create a new trail in this account
Also Read: How to Setup CloudTrail?
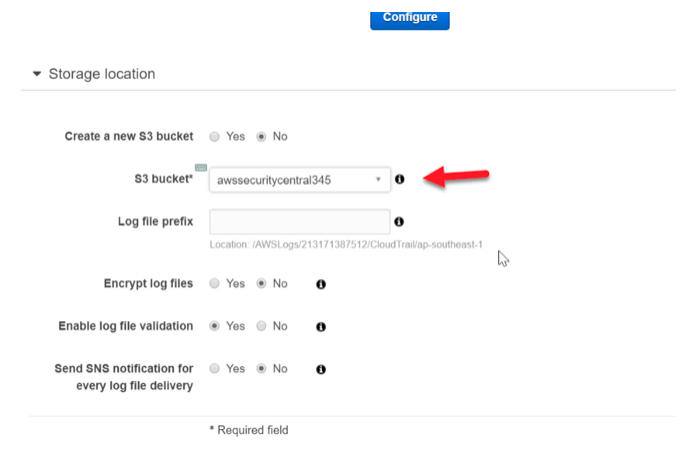
Step 5) In the configuration for the CloudTrail, ensure to enter the S3 bucket which was created earlier in the cloud-production account.
Then go ahead and save the trail.
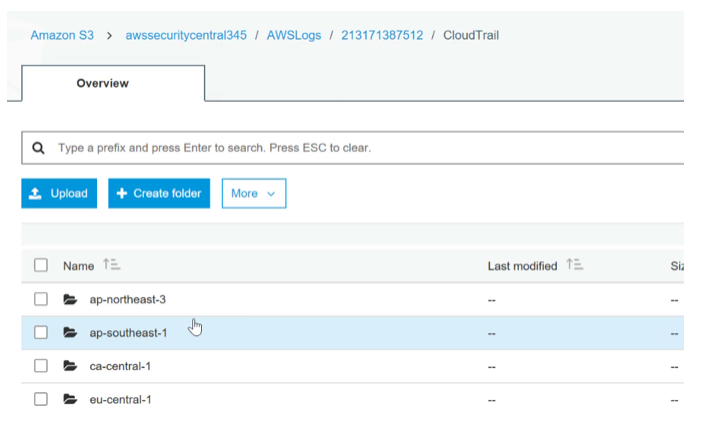
After some time, when you go back to your production account and go to the security bucket, you will see the log files for the cloud-staging account
Other Related Resources:
How to Set Right Inbound & Outbound Rules for Security Groups and NACLs?
Working with IAM and Bucket Policies
How to Grant Access to AWS Resources to the Third Party via Roles & External Id?
Summary
- When you have multiple AWS accounts, from a security perspective, its good to have all the logs directed to a central account
- In the central account, create a bucket to hold the logs
- Ensure a bucket policy is in place to provide access to all other accounts the ability to add objects to the central S3 bucket
- Then create a trail in each account and ensure that the bucket name is specified in the cloud trail
- This is the procedure of using Central CloudTrail S3 Bucket for Multiple AWS Accounts
So, how’s your preparation going for AWS Certified Security Specialty exam? Hope this topic will help you understand the concepts and take your exam preparation one level up. Check your preparation level and give your preparation a new edge with AWS Certified Security Specialty practice tests. This practice tests series has been curated to help you prepare for the exam and get ready to pass the exam in the first attempt.
Seeking any help/assistance for your AWS Certified Security Specialty exam preparation? Write us in the comment below or reach us at Whizlabs Helpdesk, we’ll be happy to help you.
- Top 20 Questions To Prepare For Certified Kubernetes Administrator Exam - August 16, 2024
- 10 AWS Services to Master for the AWS Developer Associate Exam - August 14, 2024
- Exam Tips for AWS Machine Learning Specialty Certification - August 7, 2024
- Best 15+ AWS Developer Associate hands-on labs in 2024 - July 24, 2024
- Containers vs Virtual Machines: Differences You Should Know - June 24, 2024
- Databricks Launched World’s Most Capable Large Language Model (LLM) - April 26, 2024
- What are the storage options available in Microsoft Azure? - March 14, 2024
- User’s Guide to Getting Started with Google Kubernetes Engine - March 1, 2024