Preparing for a Cloud Security interview? Here we’ve compiled a list of top Cloud Security Interview Questions with detailed answers. Go through these Cloud Security interview questions and get yourself ready for the interview!
Cloud computing has become a revolution now, and it has been growing ever since its inception. While the IT industry is keen on hiring individuals who are experts in this field, they are also looking for ways to improvise the technicalities involved. Just as cloud computing is a boon, therefore saving it from external disruptions is also important. Here comes cloud security, thus.
Try Now: AWS Certified Security Specialty free practice test
Cloud Security Interview Questions and Answers
Cloud computing security or simply cloud security is a set of rules and regulations that control the functioning of cloud computing in order to safeguard the data, applications and other relevant infrastructures of cloud computing.
With the advent of such newer technologies, and owing to their list of advantages, there has been a growth in job opportunities too in cloud computing and security.
This blog is primarily focused on the Cloud Security Interview Questions for freshers that will help as well as an experienced individual to prepare for the interview ahead and thus, face the interviewer with confidence.
1. Why should you use cloud computing?
Answer: The main advantages of using cloud computing can be listed below in the following points:
- It increases productivity
- It is cost effective and saves time
- It is an easy and secure data storage
- It is useful for data backup
- It has powerful servers
- It also has sandboxing capabilities
2. List the three basic clouds in cloud computing.
Answer: The three basic clouds in cloud computing are Professional Cloud, Performance Cloud, and Personal Cloud.
3. What are the general characteristics of cloud computing?
Answer: The basic characteristics of cloud computing are as follows:
- Elasticity and scalability
- Standardized interfaces
- Billing self-service based usage
- Self-service provisioning
- Automatic de-provisioning
Preparing for AWS Certified Security Specialty exam? Here is the comprehensive AWS Certified Security Specialty preparation guide that will help you to prepare and pass the certification exam.
4. What are the components of a server computer in cloud computing?
Answer: The basic components of a server computer include Motherboard, Hard drives, Memory, Network Connection, Processor, Video, and Power Supply and so on.
5. What are the platforms for using large-scale cloud computing?
Answer: The platforms for large-scale cloud computing are: Apache Hadoop and Map Reduce.
Apache Hadoop – It is an open source platform written in Java. It creates a pool of computer with each file system. Then the data elements are clustered and similar hash algorithms are applied. Then copies of the existing files are created.
Map Reduce – It is a software built by Google in order to support distributed computing. It uses a large set of data and various cloud resources and then distributes the data to several other computers known as clusters. Map Reduce can deal with both structured and unstructured data.
6. What security aspects do you receive along with cloud?
Answer: There are mainly two security aspects of cloud, these are –
- Authentication and authorization, and
- Control of access.
The former allows only those users who are genuine, to access that data and applications. Whereas, the latter aspect permits the users to control the access of other users who may try to enter into the cloud environment.
This is one of the common Cloud security interview questions that you will definitely encounter this question during your search for Google cloud questions and answers.
7. How can you deploy cloud computing with different models?
Answer: Various models are used for deployment in cloud computing. They are as follows: Private Cloud, Public Cloud, Hybrid Cloud, and Community Cloud.
8. What are the precautions that a user must consider before going for cloud computing?
Answer: The precautions that a user must take before going for cloud computing are as follows:
- Integrity of data
- Loss of data
- Data storage
- Continuity of business
- Compliance with the rules and regulations
- Uptime
9. Can you name some open source cloud computing platform databases?
Answer: The three main open source cloud computing platform databases are Couch DB, Lucid DB, and Mongo DB. (DB stands for database)
This is one of the frequently asked cloud security interview questions that you may probably come across during the interview. You should name the cloud computing platform databases that you have worked upon as the interviewer may ask some more questions on those databases.
10. Can you differentiate between computing for mobiles and cloud computing?
Answer: Although, both of these use the same concept, yet they differ in some instances. In the case of cloud computing, it is activated via the internet instead of the individual device. This facilitates the user to retrieve data on demand. On the other hand, the mobile runs applications on the remote server and therefore lets the user access the storage and manage accordingly.
Are you an AWS Security professional? AWS Security Specialty certification recognizes and demonstrates your expertise in AWS Security. Plan now to validate your skills with the AWS Certified Security Speciality exam!
11. What can a user gain from utility computing?
Answer: The main advantage of utility computing is that a user pays for only what he uses. It is like a plug-in that is managed by the organization which decides on the type of services to be deployed from the cloud.
It is one of the most common questions among the Cloud Security Interview Questions that you should be prepared with, to pass your cloud security interview.
12. Do you know the security laws that are implemented to secure data in the cloud?
Answer: There are a total of five main security laws that are generally implemented. They are:
- Validation of input: The input data is controlled.
- Backup and security: The data is secured and stored and thus controls data breaches.
- Output reconciliation: The data is controlled which is to be reconciled from input to output.
- Processing: The data which is processed correctly and completely I an application, is controlled.
13. Define cloud computing in layman language.
Answer: It is the computing based on the internet. Here, the internet is used to process and deliver the services to the users as and when required. Several companies are resorting to cloud computing now in order to fulfill the needs of the customers, business leaders or providers.
The resources are thus treated as a pool herein, and not as resources that are independent.
14. Can you name some large cloud providers and databases?
Answer: The three large cloud providers and databases are:
- Cloud-based SQL
- Amazon Simple Database
- Google Bigtable
15. How is cloud different from traditional data centers?
Answer: This is one of the common Cloud security interview questions that you will definitely encounter during your search for Google cloud questions and answers. You may answer this question in the following manner. The traditional data centers are expensive owing to the factor that the heating of hardware or software. And most of the expenses are spent on the maintenance of the data centers, but this is not the case in cloud computing. In the case of the cloud, the data can be stored easily and does not require as much expense with their maintenance.
16. What is cloud architecture?
Answer: It is the main question in the case of network security interview questions and answers. Cloud architecture is the combination of both components along with the subcomponents that are required for cloud computing.
Both the front end and back end platforms are there which include the clients, mobile device, server, and storage in all. Other than these, a network and a cloud-based delivery are also there.
17. Name the building blocks of cloud architecture.
Answer: There are essentially three building blocks in the cloud architecture.
The first is the Reference Architecture; next is Technical Architecture and the last is Deployment operation Architecture.
18. Define the different layers of cloud architecture.
Answer: There are five layers of cloud architecture, and they are as follows:
- Cloud Controller (CLC)
- Storage Controller (SC)
- Node Controller (NC)
- Cluster Controller
- Walrus
19. What are the business benefits that can be derived from cloud architecture?
Answer: The benefits of cloud architecture are mentioned below:
- In time infrastructure
- Efficient utilization of resources
- Zero infrastructure investment
20. How do you secure your data while transferring on the cloud?
Answer: In order to secure the data while transferring on the cloud, it is to be checked that there is no leakage as such, and therefore encryption key must be implemented with the data that is being sent.
Preparing for Certificate of Cloud Security Knowledge (CCSK) exam? Follow this Certificate of Cloud Security Knowledge (CCSK) preparation guide and get ready to pass the exam.
21. What are the phases involved in cloud architecture?
Answer: The different phases involved in cloud architecture are four in number and they are listed below:
- Launch Phase
- Monitor Phase
- Shutdown Phase
- Cleanup Phase
22. List the components needed in cloud architecture?
Answer: There are five main components of cloud architecture. They are:
- Cloud storage services
- The speed of the Processor
- Intracloud communications
- Cloud storage services
- Cloud ingress
You are likely to be asked this during an interview on cloud computing, therefore prepare it along with other Cloud Security Interview Questions.
23. How is the cloud architecture different from the traditional architecture?
Answer: The most remarkable characteristics that distinguish the cloud architecture from the traditional architecture are mentioned below:
- Cloud architecture can scale the resources on demand, which is absent in the traditional architecture.
- It is also capable of handling dynamic workloads without any failure.
- Finally, cloud architecture also provides the required hardware.
You may probably come across this type of comparison based questions among the Cloud security interview questions for your cloud security interview.
24. How does it provide automation and transparency in performance?
Answer: There are various tools available for this purpose. Cloud architecture allows the management and also prepares reports of the work after proper monitoring of the same. It also allows the sharing of the applications. Alongside, automation is the vital component and thus it makes up for the improvement of the quality of services.
Are you a beginner aspired to build a career in the cloud security? Read our previous blog on Beginner’s Guide to Cloud Security and step into the world of cloud security.
25. What do system integrators do in cloud computing?
Answer: The system integrators of cloud computing provide the strategy of complicated processes that are used in designing a cloud platform. Owing to the fact that integrators have the knowledge of data center creation, they are likely to help in developing both public and private cloud network even more accurately.
This question is likely to be a part of cloud security interview questions and answers. So, prepare yourself with the answer so that you can handle it during the interview.
26. What is ‘EUCALYPTUS’?
Answer: It is the acronym for Elastic Utility Computing Architecture for Linking Your Programs.
27. How is EUCALYPTUS (Elastic Utility Computing Architecture for Linking Your Programs) used in cloud computing?
Answer: Eucalyptus is mainly an open source software infrastructure which is used in cloud computing. It is usually used in implementing clusters in the cloud computing platform, in order to build public, hybrid and private clouds.
It can also produce its own data center into a private cloud and therefore, you will be allowed to use its functionalities to other organizations as well.
28. Why is a virtualization platform needed in implementing cloud?
Answer: virtualization is required in the implementation of the cloud due to the following reasons:
- Cloud operating system
- In order to manage the service policies
- In order to keep the backend level and user level concepts different from each other.
Virtualization is a very essential concept in cloud computing, therefore it is quite obvious to prepare for this while preparing other Cloud Security Interview Questions.
29. What are the various data centers deployed for cloud computing?
Answer: Mainly two types of data centers are there for cloud computing, firstly low-density data centers, and secondly, containerized data centers.
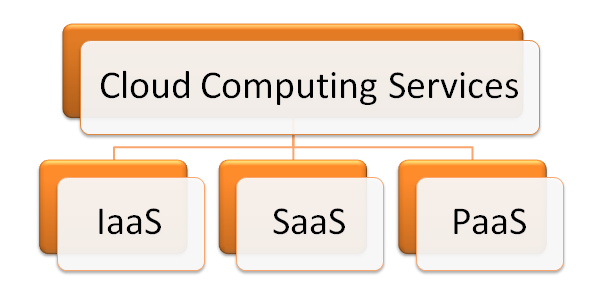
30. Name the different layers of cloud computing.
Answer: The different layer of cloud computing are as follows:
SaaS: It is Software as a Service, and provides the users a direct access to the cloud application without the need of installing them on the computer.
PaaS: It is Platform as a Service, and thus provides the application platform for the developers.
IaaS: It is Infrastructure as a Service, and provides the infrastructure to the users in terms of hardware, such as the speed of the processor, memory, etc.
31. What are the applications of cloud computing?
Answer: Cloud computing is a very speedy application process. Since you do not need to sell or buy anything in it; you can use the software in a convenient manner. The process of application building through this is 5 times faster and the applications can be deployed at anytime and anywhere. Additionally, it also instantly makes the applications mobile in nature. This is a common question that lies in the list of cloud computing interview questions as well as in the cloud security interview questions.
32. What are the benefits of cloud computing?
Answer: The main benefits of cloud computing are that it is cost effective in nature, it increases the productivity by about 50%, and reduces IT support to 40%. It also saves time to about 30%, the required power is less, and also takes up lesser space.
New in the world of cloud computing? Let’s start with this introduction to cloud computing and know the reason behind its growing importance.
Certifications play an important role in one’s career. We at Whizlabs understand the importance of certifications and thus bring AWS Certified Security Specialty Practice Tests and Certificate of Cloud Security Knowledge (CCSK) Practice Tests for you.
33. What are the different modes of SaaS?
Answer: There are two modes in Saas, and they are Fine grain multi-tenancy and simple multi-tenancy. In the case of the former, the resources are shared by many with the functionality remaining the same. On the other hand, in the latter case, every user has an independent resource and thus differs from other users. This is the reason why simple multiple tenancies are considered the most efficient mode.
Such platforms are the main component in AWS, thus, when you prepare for an interview on this topic, makes sure you study Cloud Security Interview Questions too.
34. What is the importance of PaaS?
Answer: Platform as a Service or PaaS is very important in cloud computing. It provides the application platform for the providers. It facilitates the user with complete virtualization of the infrastructure layer and finally making it function like a single server.
35. What are the resources provided in IaaS?
Answer: Infrastructure as a Service or IaaS provides the physical and virtual resources which are used to build a cloud, to the user. This layer of computing deals with the complexities of deployment and maintenance of the services provided by the same layer. The infrastructures consist of the servers, the hardware systems, and storage.
36. Define cloud service.
Answer: This is the basic question you will come across in any cloud-related interview whether be the cloud computing interview questions or the cloud security interview questions. A cloud service basically builds cloud applications. In simple words, one can use the applications even without installing them on the computer. As a result, the maintenance and support of the application are not required as compared to those applications that need to be installed on the computer in order to use them.
37. List the main features of cloud service.
Answer: The main features of the cloud service are mentioned below:
- Development of applications that can manage several clients at a time.
- Centralization of the update feature of the software which will eliminate the need of downloading the updated versions.
- Centralization of the activities of software management in the Web environment.
- Access and management of the commercial software.
38. How is API used in cloud services?
Answer: API is Application Programming Interface. It is a very useful component in cloud platforms. It is used in the following ways:
- It instructs the communication between one or more applications.
- It allows the creation of applications in an easy manner, along with the linking of cloud services with other systems.
- It also eliminates the need for writing the full programs.
39. Why is it advantageous to use cloud services?
Answer: The cloud services are used due to the following reasons:
- It helps in developing scalable and robust applications since scaling is much faster now.
- Therefore, it saves the time of deployment and also maintenance.
- It facilitates the utilization of investment in the corporate sector.
- It is cost effective also.
40. Define scalability and elasticity in terms of cloud computing.
Answer: Scalability and elasticity are both characteristics of cloud computing. The former is handled by increasing the proportion of the amount of resource capacity. On the other hand, the latter highlights the concept of commissioning and also decommissioning of a large amount of resource capacity.
Cloud features and characteristics are very important in cloud computing, therefore it is quite obvious to prepare for this type of questions while preparing other Cloud Security Interview Questions.
New in the world of Cloud Security? Here we bring the beginner’s guide to Cloud Security that will help you understand the basics of cloud security to build a career in it.
41. What is the role of the performance cloud in cloud computing?
Answer: The performance cloud helps to transfer the maximum amount of data instantly. It is generally used by professionals who work with high-performance research in computing.
It is no wonder that you will be asked about the role of cloud performance in computing in the Cloud Security Interview Questions.
42. What are hybrid and community clouds?
Answer: Hybrid cloud, as the name suggests; it is composed of both public and private clouds. Therefore a hybrid has multiple service providers. For instance, a company might want to implement SaaS application throughout; therefore the required security will be provided by the firewall (private cloud) and the additional security will be provided by VPN (public cloud)
On the other hand, a community cloud service is used by different companies together when they are ready to share the benefits of the cloud. As the cloud provides benefits of both privacy and security, companies having the same requirements often agree on sharing the same.
43. Do you know Amazon about SQS?
Answer: In order to connect with various connectors, Amazon SQS message is used between various components of Amazon. Therefore, it can be said that Amazon SQS acts as a communicator.
44. How is buffer used in Amazon Web Services?
Answer: A buffer is used to make systems more efficient against the traffic or load. It helps in the synchronization of different components. The buffer helps in maintaining the balance between those components and also makes them work at the same speed in order to get the work done faster.
You are likely to come across this question during AWS cloud security interview questions. So, whenever you go for an AWS cloud interview, don’t forget to cover this type of AWS security questions.
45. What are the optimization strategies involved in the cloud?
Answer: The optimization strategy is very interesting. In order to overcome the cost of maintenance and optimizing the resources, there is a three data center concept in cloud computing. This provides recovery and also backup in case of any system failure or disaster, thereby keeping the data safe and secured.
46. Why do you think an organization needs to manage the workloads?
Answer: Workloads specifically means an independent set of codes or instructions that can be executed to perform a specific task. It can be either a part of the application or the complete application itself. Therefore, an organization is likely to manage these due to the following reasons:
- In order to know that whether the applications are running properly.
- In order to know the functions, they are performing.
- In order to know the changes in the individual department with respect to the service provided.
47. What do you know about Windows Azure OS?
Answer: The Windows Azure Operating System is specifically used in order to run the applications on the Windows Azure Platform. The OS consists of all the necessary prerequisites for running the applications and hosting them on the cloud. The operating system is known to provide development of services before they are deployed on the Windows Azure in the cloud.
The OS also provides some other features of Web computational services, storage services, management services, load balancers, and many more.
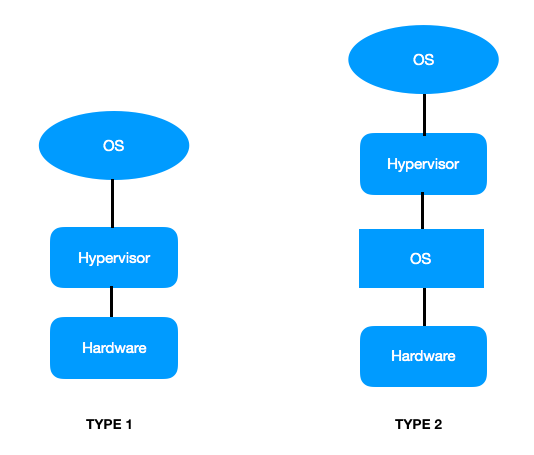
48. What is the Hypervisor in cloud computing?
Answer: it is the most important question among cloud security architect interview questions. A hypervisor is a virtual machine monitor. It helps in the management of virtual machines. Generally, there are two types of hypervisors. They are:
Type 1 – in this case, the guest VM directly runs over the host hardware.
Type 2 – in this case, the guest VM runs over the hardware through a host operating system.
It is no wonder that you will be asked about the hypervisor in the Cloud Security Interview Questions.
49. What is the importance of cloud computing in IT?
Answer: The IT sector has been booming and cloud computing has just taken over the world with its benefits. Starting from services like faster application building to immense storage spaces and easier delivery of services, the cloud computing has become the backbone of the IT now.
50. It is said, ‘cloud computing can save money’. What is your view?
Answer: The interviewer may ask this type of statement based cloud security interview questions in the interview to check the knowledge and attentiveness of the candidate. And the answer should be like – the foremost benefit and best thing about cloud are that you do not need to buy the cloud. It is already there by virtue. Therefore, the infrastructure already exists, and you only have to take advantage of the same for your benefit. As a result, you only pay for your use, and then simply turn it off.
Final Words
The boom of cloud computing is expanding tremendously, and thus the value of cloud security. It brings a number of opportunities for the cloud professionals in this era of technology. We’ve compiled this set of cloud security interview questions to help you crack the interview in the first go. However, in this world of competition, the certifications become very important and we can’t ignore it.
So, if you are aspired to crack the interview, then demonstrate your cloud security knowledge to your interviewer during the cloud security interview with a cloud security certification. That will prove an important tool just like these cloud security interview questions.
Want to get a boost in your cloud security career? Bring your career one level up with the Certificate of Cloud Security Knowledge (CCSK certification) or AWS Certified Security Specialty certification. Start your preparation now with Whizlabs CCSK Practice Tests and AWS Security Specialty practice tests.
If you have any queries regarding cloud security, don’t hesitate to put them below in the comment box, we’ll be happy to help you.
Good luck with your Cloud Security interview!
- Top 20 Questions To Prepare For Certified Kubernetes Administrator Exam - August 16, 2024
- 10 AWS Services to Master for the AWS Developer Associate Exam - August 14, 2024
- Exam Tips for AWS Machine Learning Specialty Certification - August 7, 2024
- Best 15+ AWS Developer Associate hands-on labs in 2024 - July 24, 2024
- Containers vs Virtual Machines: Differences You Should Know - June 24, 2024
- Databricks Launched World’s Most Capable Large Language Model (LLM) - April 26, 2024
- What are the storage options available in Microsoft Azure? - March 14, 2024
- User’s Guide to Getting Started with Google Kubernetes Engine - March 1, 2024


I jumped to the interview questions while i got no idea about Cloud Computing. I would appreciate if i got a tutorial on Cloud Computing and Virtualization Service.. I thank you in advance…
Thanks for writing this compiling this awesome article. I am very much appreciated by your FAQ’s. It really helped me clear my interview with Cloudways.
I applied their for the position of Cloud architect and they asked me several questions around Cloud security as they highly focus on the security of data.
You can’t see so many companies nowadays who focus that much on the security of their customers data. Facebook incident is the live example of it but, I saw a completely changed atmosphere over there.